Deployment: Invicti Platform on-demand, Invicti Platform on-premises
Webhook integration
Integrating Invicti Platform with a webhook endpoint enables real-time notifications triggered by scan events or vulnerability discoveries. You can deliver data directly to any internal tool, ticketing system, or custom application that accepts HTTP requests. The configuration is the same whether you use the webhook as a Team communicator or an Issue tracker. The only difference is which placeholder fields are substituted in the payload.
Prerequisites
To set up this integration, you need:
- A publicly reachable HTTP/HTTPS endpoint that can receive HTTP requests from Invicti. The integration supports POST, GET, and PUT methods. If your endpoint requires authentication, Basic authentication (username and password) is supported.
Multiple integrations for different notification types
You can create multiple webhook integrations to route notifications to different endpoints. Each integration targets one webhook URL. Consider these example configurations:
- Critical vulnerabilities: a dedicated integration posting to your incident management system for critical findings
- All vulnerabilities: a broader integration posting to your central logging or SIEM platform
This allows you to configure different notification rules based on:
- Severity levels: Critical, High, Medium, Low, Informational
- Specific targets, collections, or applications
Step 1: Configure Invicti Platform integration
-
In Invicti, select Integrations from the left-side menu.
-
Switch to the Browse integrations tab.
-
Find the Webhook tile - it appears under both Team communication and Issue trackers - and select Configure.
-
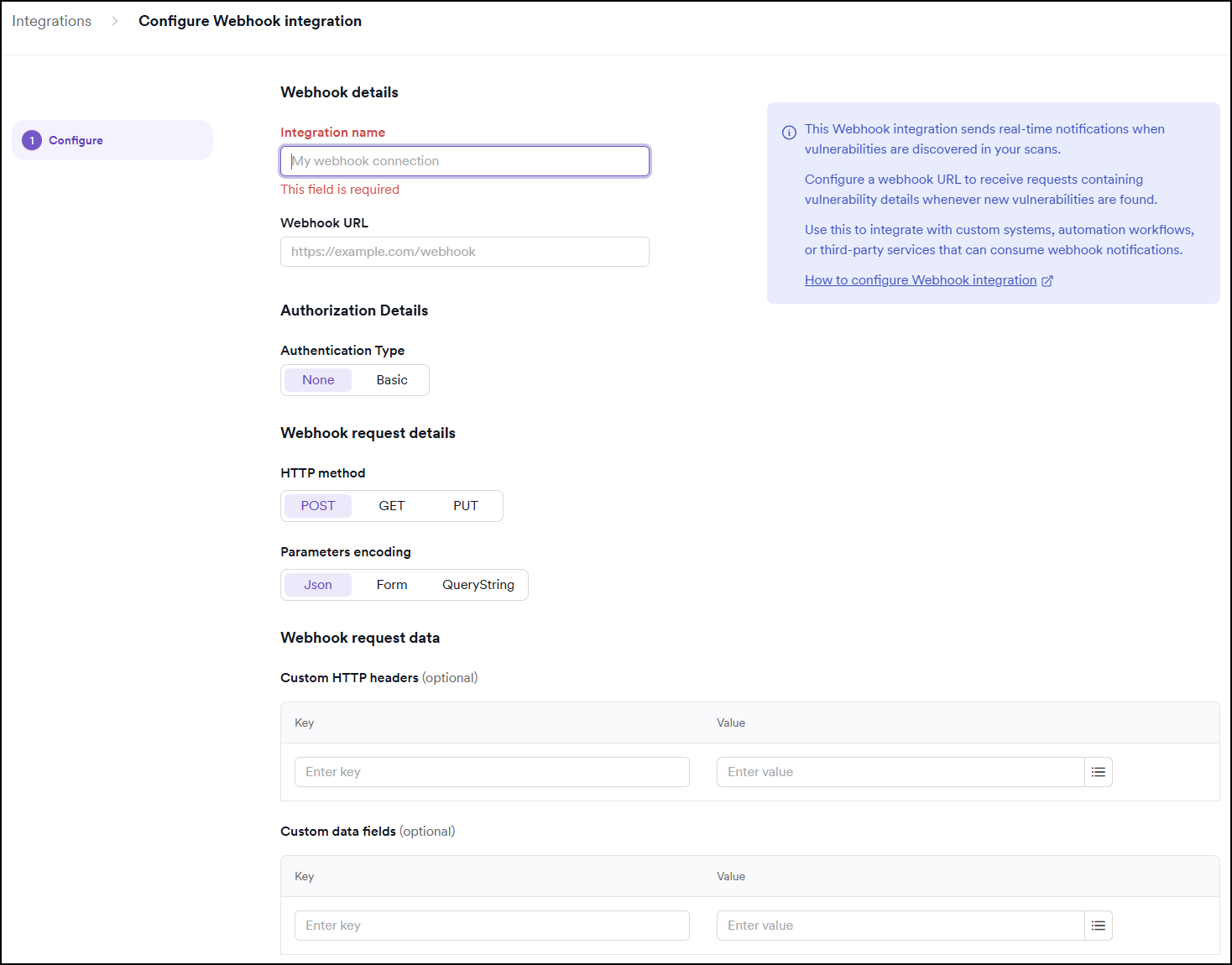
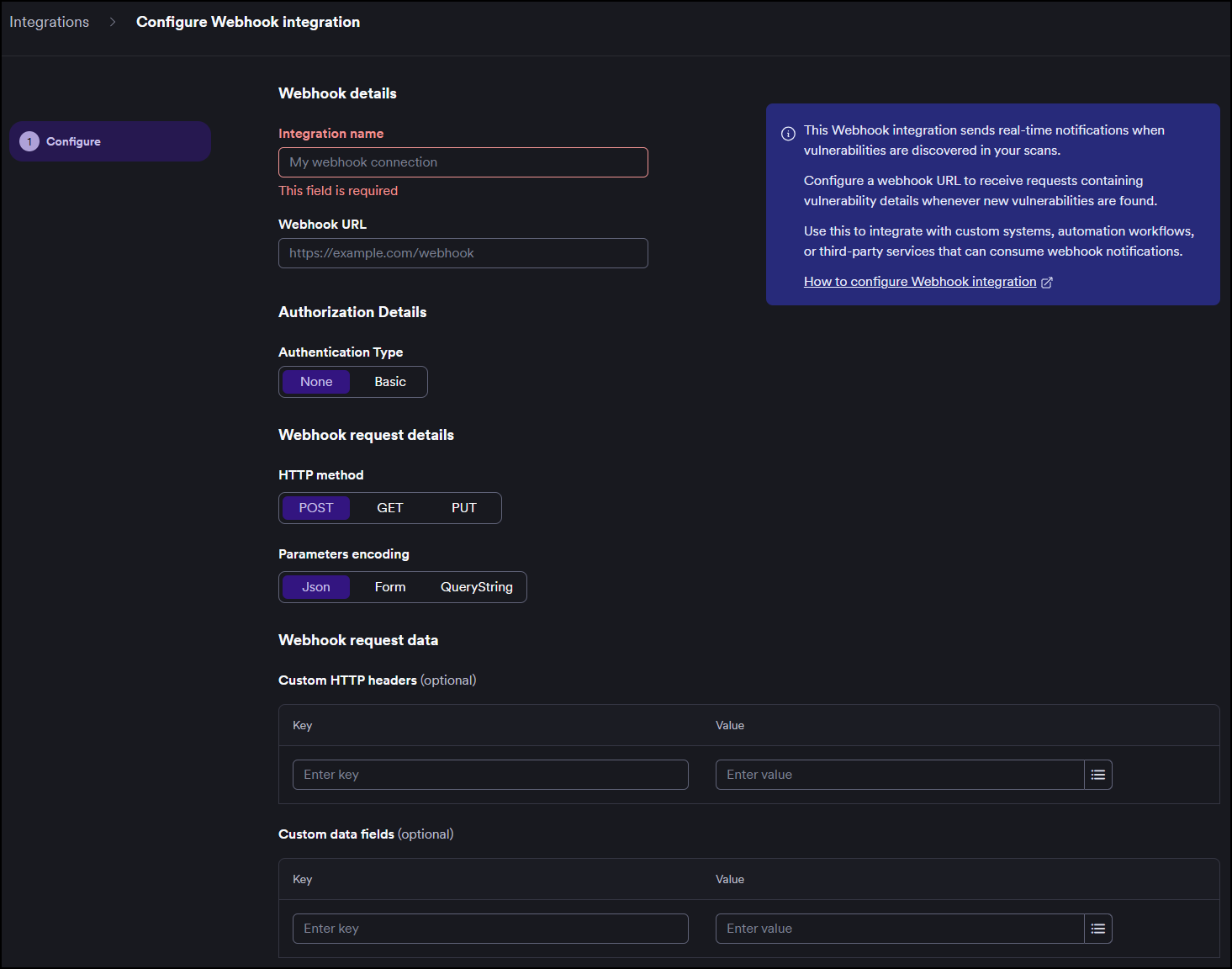
Under Webhook details:
- Enter an Integration name.
- Enter your Webhook URL (must be a valid HTTP or HTTPS URL, for example
https://example.com/webhook).
-
Under Authorization Details, choose an Authentication Type:
- None: (default) no authentication required.
- Basic: enter your username and password.
-
Under Webhook request details:
- Choose the HTTP method: POST (default), GET, or PUT.
- Choose Parameters encoding: Json (default), Form, or QueryString.
-
Under Webhook request data, optionally configure:
- Custom HTTP headers: add any headers your endpoint requires as key-value pairs (for example,
X-Api-Key/your-token). - Custom data fields: map Invicti placeholder fields to the payload structure your endpoint expects. See Payload customization below for details.
- Custom HTTP headers: add any headers your endpoint requires as key-value pairs (for example,
-
Click Send test webhook to verify your configuration. Your endpoint receives a test vulnerability notification.
-
Click Save and finish to complete the integration.
-
The Webhook integration is now visible in the list of My integrations.
Retry behavior
If your endpoint doesn't return a 200 response, Invicti retries the webhook up to 3 times. Retries are triggered on server errors (5xx). Client errors (4xx) are not retried — a 4xx response is treated as a permanent failure.
Payload customization
You can fully customize the data your webhook endpoint receives. Use Custom data fields in the form to map Invicti placeholder fields to whatever structure your endpoint expects.
Which fields are actually substituted depends on the automation event the webhook is used with:
| Use case | Automation event | Fields substituted |
|---|---|---|
| Team communicator | Scan completed, Scan failed | Scan fields |
| Issue tracker | Vulnerability found | Vulnerability fields, Asset fields |
All placeholder fields are always visible in the Custom data fields table regardless of which use case you configure. If you map a field that does not match your integration's context, the placeholder is not replaced. Your endpoint receives the literal text (for example, {Vulnerability ID}) instead of an actual value.
If you configure Vulnerability fields in a webhook used as a Team communicator, those placeholders won't be substituted. Your endpoint receives the literal placeholder text instead of actual values. The same applies in reverse for Scan fields used in an issue tracker context.
Placeholder fields for issue trackers
Use these fields when the webhook is triggered by Vulnerability found events.
Vulnerability fields
| Placeholder | Description | Type |
|---|---|---|
{Vulnerability} | Vulnerability name | string |
{Vulnerability ID} | Unique vulnerability identifier | string |
{Vulnerability type ID} | Type identifier | string |
{Description} | Detailed description | string |
{Details} | Additional details | string |
{Recommendation} | Remediation recommendations | string |
{Severity} | Severity level (info, low, medium, high, critical) | string |
{References} | Related references and links | string |
{Affected URL} | URL where the vulnerability was detected | string |
{Confidence} | Detection confidence level | number |
{CVSS Score} | CVSS v2 score | number |
{CVSS3 Score} | CVSS v3 score | number |
{CVSS4 Score} | CVSS v4 score | number |
{Impact} | Impact description | string |
{Vulnerability Link} | Link to vulnerability details in Invicti | string |
Asset fields
| Placeholder | Description | Type |
|---|---|---|
{Asset ID} | Unique asset identifier | string |
{Asset name} | Name of the asset | string |
{Asset type} | Type of asset | string |
{Business impact} | Business impact value | string |
{Asset Description} | Description of the asset | string |
Placeholder fields for Team communicators
Use these fields when the webhook is triggered by Scan completed or Scan failed events.
Scan fields are not yet documented here. Contact your Invicti representative or check the Help Center for the current list of available scan placeholder fields.
Payload formatting examples
Flat structure
Map placeholders directly to top-level field names:
{
"vuln_id": "{Vulnerability ID}",
"title": "{Vulnerability}",
"severity": "{Severity}",
"url": "{Affected URL}",
"asset": "{Asset name}"
}
Your endpoint receives:
{
"vuln_id": "...",
"title": "...",
"severity": "high",
"url": "https://example.com/login",
"asset": "Production App"
}
Nested objects
Wrap the key in braces and use dot notation to create nested JSON:
{
"{data.vulnerability.id}": "{Vulnerability ID}",
"{data.vulnerability.name}": "{Vulnerability}",
"{data.vulnerability.severity}": "{Severity}",
"{data.asset.name}": "{Asset name}",
"{data.asset.type}": "{Asset type}"
}
Your endpoint receives:
{
"data": {
"vulnerability": {
"id": "...",
"name": "...",
"severity": "high"
},
"asset": {
"name": "Production App",
"type": "..."
}
}
}
Arrays
Use index notation [0], [1], etc., to build arrays:
{
"{vulnerabilities[0].id}": "{Vulnerability ID}",
"{vulnerabilities[0].severity}": "{Severity}",
"{vulnerabilities[0].url}": "{Affected URL}",
"{tags[0]}": "security",
"{tags[1]}": "invicti"
}
Your endpoint receives:
{
"vulnerabilities": [
{
"id": "...",
"severity": "high",
"url": "https://example.com/login"
}
],
"tags": ["security", "invicti"]
}
Mixed flat and nested keys
You can combine regular field names with templated nested keys in the same payload:
{
"id": "{Vulnerability ID}",
"severity": "{Severity}",
"{details.description}": "{Description}",
"{details.recommendation}": "{Recommendation}",
"asset_name": "{Asset name}"
}
Your endpoint receives:
{
"id": "...",
"severity": "high",
"details": {
"description": "...",
"recommendation": "..."
},
"asset_name": "Production App"
}
The maximum nesting depth is 10 levels. Only object keys count toward this limit — array indices do not.
{a.b.c.d.e.f.g.h.i.j}: 10 levels (at the limit){items[0][1][2].field}: 2 levels (itemsandfield)
Step 2: Configure notifications
This section provides basic instructions on how to create various automations. For more detailed instructions on how to create an automation, refer to the new automation document.
Send a webhook notification on scan completion or failure (Team communicator)
Click to expand step-by-step instructions
-
Select Automations from the left-side menu.
-
Click Add new automation.
-
In the dialog box populate these fields:
- Name: send a webhook on scan completion.
- Description: sends a webhook notification when a scan completes or fails.
- Automation scope: specify the assets or collections.
-
Click Add automation.
-
Add an event of Scan completed or Scan failed and click Save.
-
Add an action of Send to communicator and specify the correct Webhook integration.
Send a webhook notification on vulnerability found (Issue tracker)
Click to expand step-by-step instructions
-
Select Automations from the left-side menu.
-
Click Add new automation.
-
In the dialog box populate these fields:
- Name: send a webhook on vulnerability found.
- Description: sends a webhook notification to the issue tracking system when a vulnerability is discovered.
- Automation scope: specify the assets or collections.
-
Click Add automation.
-
Add an event of Vulnerability found and click Save.
-
Add an action of Create issue and specify the correct Webhook integration.
Need help?
Invicti Support team is ready to provide you with technical help. Go to Help Center