OWASP API Top Ten report
The Open Web Application Security Project (OWASP) API Top 10 is a list of top security concerns specific to web Application Programming Interface (API) security.
- APIs are a critical part of modern mobile, Software as a Service (SaaS), and web applications and expose application logic and sensitive data, so APIs have become a target for attackers.
- While general web application security best practices also apply to APIs, the OWASP API Security project has prepared a list of top 10 security concerns specific to web API security.
- Thanks to the OWASP Top Ten API report, you can identify the common weaknesses, which can be present in your web application and exploited by malicious attackers.
For more information, refer to the the OWASP API Security Top 10 article. For information on differences between 2019 and 2023 reports, refer to the OWASP API Security Top 10 2023 article.
There can be other vulnerabilities and security issues found in your web applications but not listed in the OWASP API Top Ten report. For the comprehensive security report, generate the Detailed scan report.
Click to view a sample OWASP API Top Ten 2019 report.
For other reports available in Invicti, refer to the Overview of reports, Report templates, and Built-in reports documents.
Report sections
There are five sections in the OWASP API Top Ten report. Each of them is explained in the following sections.
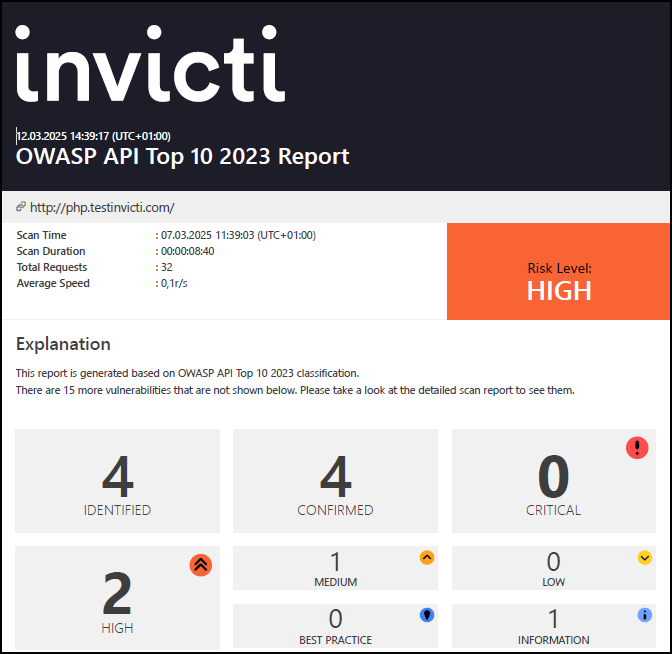
Scan metadata
This section provides details on the following items:
- Scan target: the target URL or web application being scanned.
- Scan time: when the scan was initiated.
- Scan duration: how long the scan took to complete.
- Description: additional notes or description of the scan.
- Total requests: number of HTTP requests made during the scan.
- Average speed: the average scanning speed.
- Risk level: the overall risk assessment of the target.
Vulnerabilities
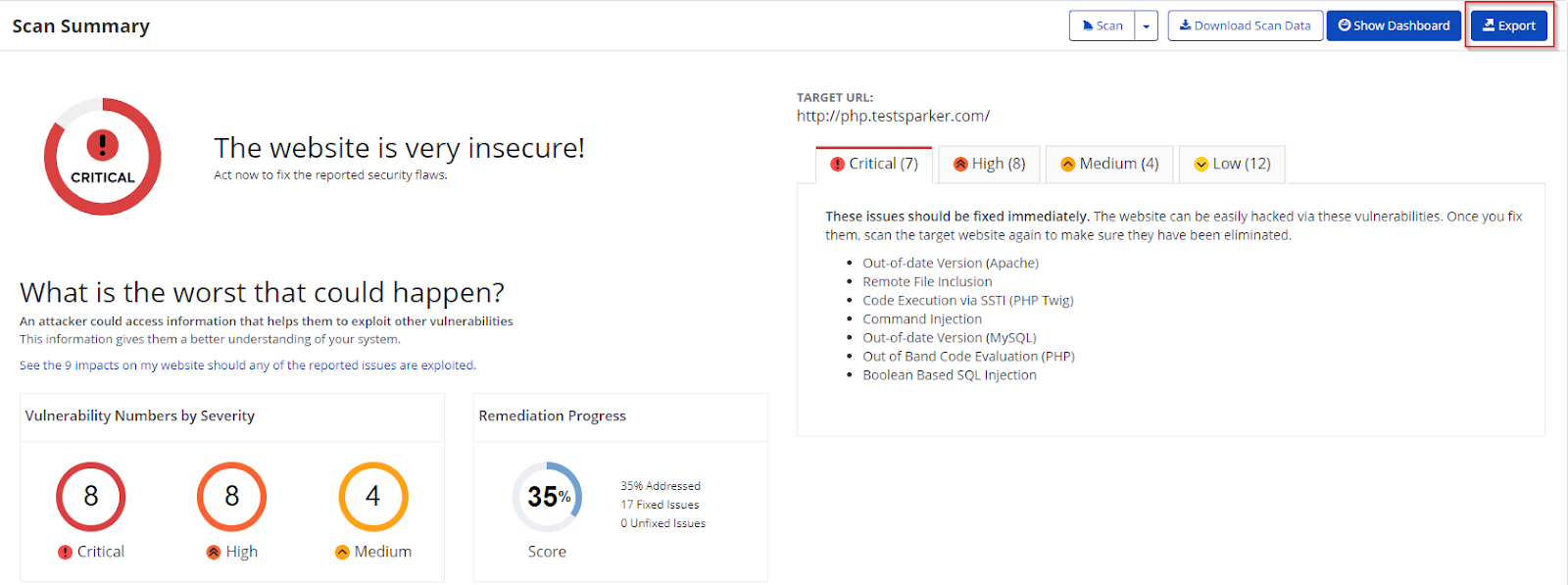
This section provides a numerical and graphical overview of:
- Numbers: the numbers of issues detected at various vulnerability severity levels.
- Identified vulnerabilities: the total number of detected vulnerabilities.
- Confirmed vulnerabilities: the total number of vulnerabilities that Invicti verified by taking extra steps such as extracting some data from the target.
Vulnerability summary
This section provides a summary of information about each discovered vulnerable URL and categorizes them based on severity. For example, if Invicti determines a vulnerability as Critical, it requires immediate attention.
If you click an identified vulnerability, you can access detailed information, such as HTTP request and response codes and body, about the vulnerability and, if any, Proof of Exploit. If Invicti finds a vulnerability but has no proof of exploit, Invicti presents a certainty degree about this issue.
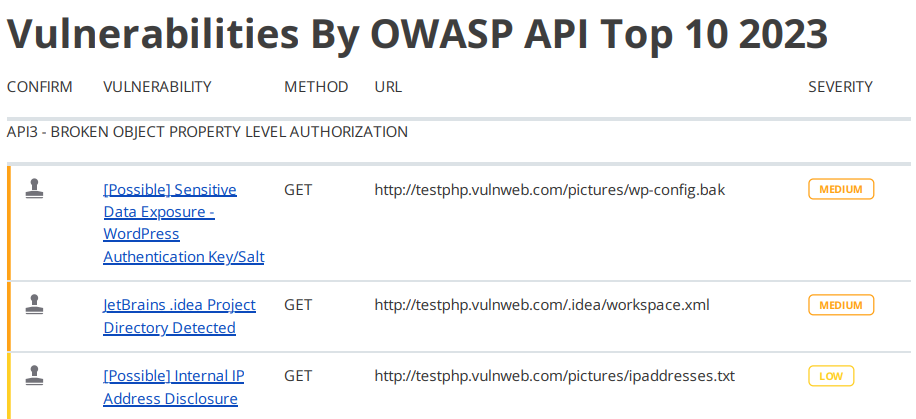
The following list explains the columns in the vulnerability summary:
- Confirm: shows whether Invicti has verified a vulnerability.
- Vulnerability: displays the name of the issue and provides a link to a detected issue that attackers can exploit.
- Method: the HTTP method of the request in which Invicti sent the payload. It demonstrates what Invicti deployed to identify an issue.
- URL: a reference to a resource that contains the issue.
- Parameter: the variable used to identify the issue.
For more information, refer to the Vulnerability severity levels document.
Vulnerability names and details
This section describes all identified issues and vulnerabilities, along with their impact and proof of exploit. It also explains what actions to take and a remedy for each one, including external references for more information.
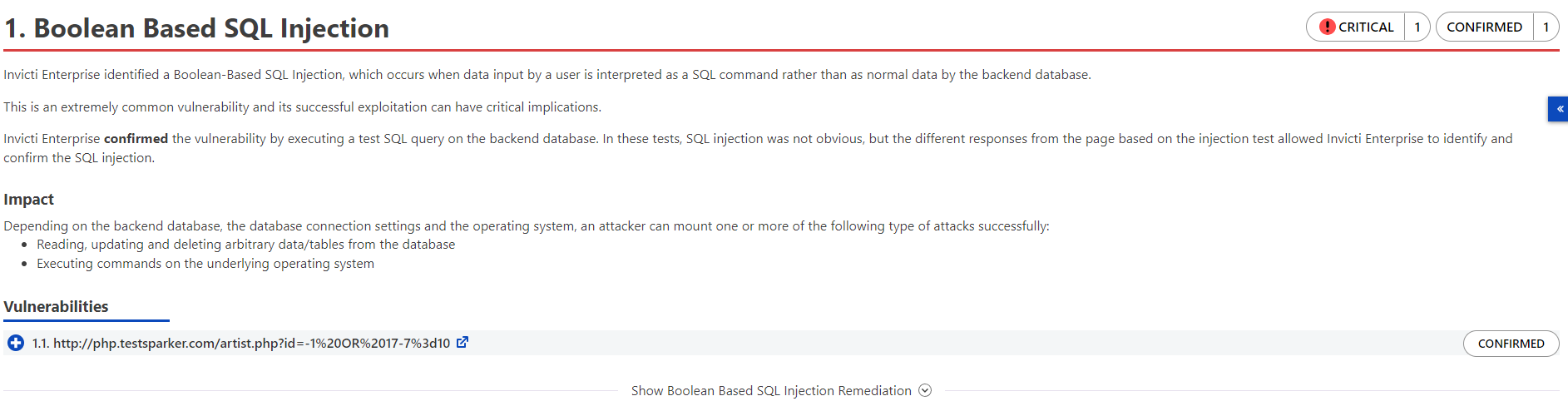
The following list explains the headings in the vulnerability names and details section:
- Name: the name of the identified issue.
- Tag: the label to group, organize, and filter issues in the target web application.
- Proof of exploit: a piece of evidence supplied to prove that the vulnerability exists, showing information that's extracted from the target using the vulnerability. For more information, refer to the Benefits of Proof-Based Scanning™ Technology document.
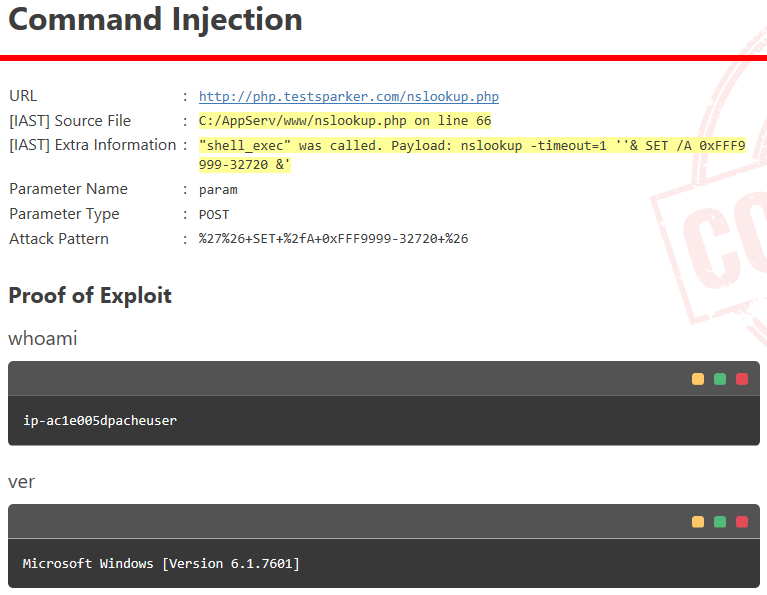
- Vulnerability details: displays further details about the vulnerability.
- Certainty value: indicates how much Invicti is sure about the identified issue.
- Impact: shows the effect of the issue or vulnerability on the target URL.
- Required skills for successful exploitation: details on how malicious hackers could exploit this issue.
- Actions to take: the immediate steps you can take to decrease the impact or prevent exploitation.
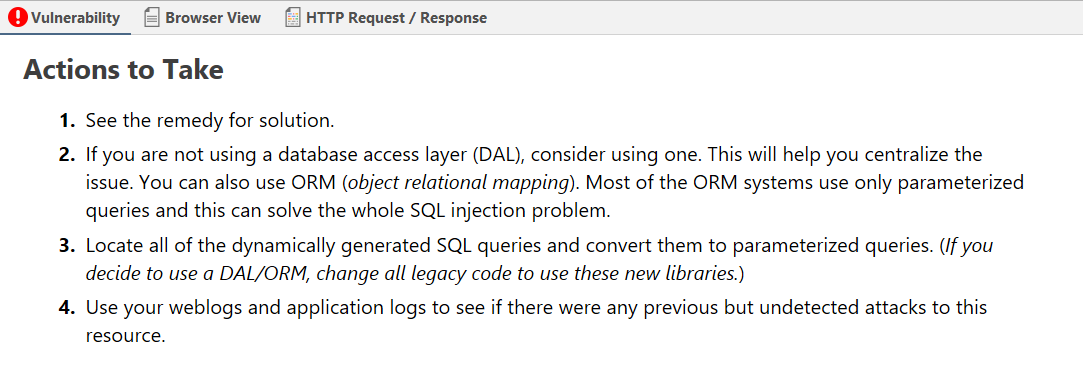
- Remedy: further steps to resolve the identified issue.
- External references: links to other websites where you can find more information.
- Classification:
- CVSS 3.0: shows the severity score of vulnerability based on the 3.0 edition of the Common Vulnerability Scoring System.
- CVSS 3.1: shows the severity score of vulnerability based on the 3.1 edition of the Common Vulnerability Scoring System.
- OWASP API Top Ten 2019 or 2023: provides further information about this vulnerability according to the 2019 or 2023 edition of the Open Web Application API Security Project (OWASP) Top 10 list.
- Remedy references: further information on the solution for identified issues.
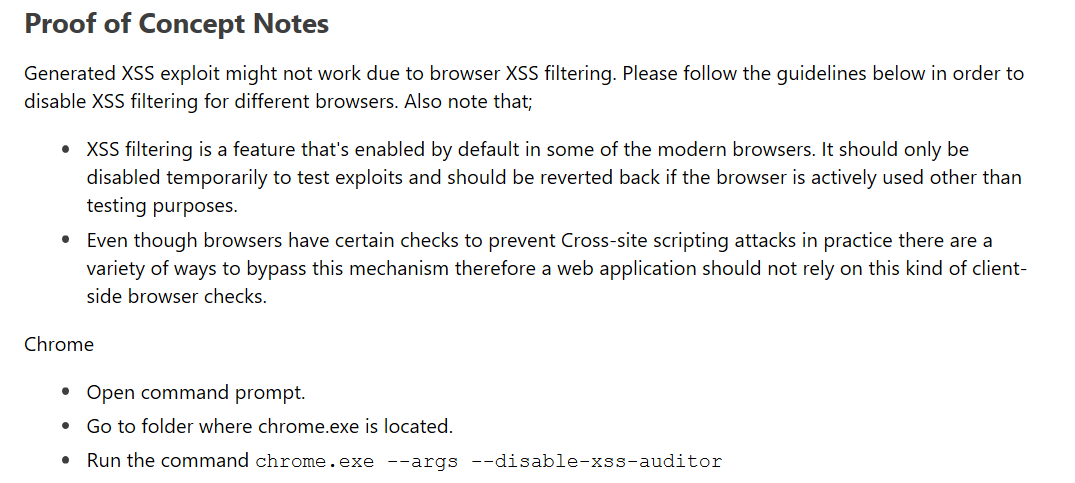
- Proof of concept notes: notes that demonstrate in principle how a system may be compromised.
- Request: the whole HTTP request that Invicti sent to detect the issue.
- Response: the reply from the system against the payload.
Show/hide scan details
This section provides some profile and policy settings that Invicti uses to adjust its scanning to reach more coverage. For example, it lists all enabled security checks.
It provides information on your preference in selecting this scan so that developers have more details on how this scan was run.
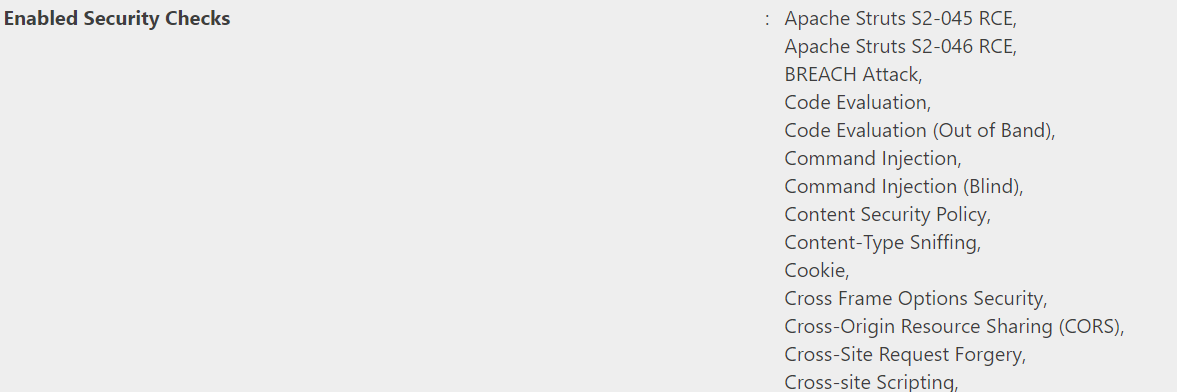
For more information, refer to the Security checks document.
Generate an OWASP API Top Ten report in Invicti Enterprise
- Select Scans > Recent Scans from the left-side menu.
- Next to the relevant scan, choose Report.
- On the Scan Summary page, choose Export.
- From the Report dropdown, choose OWASP API Top Ten 2019 or OWASP API Top Ten 2023.
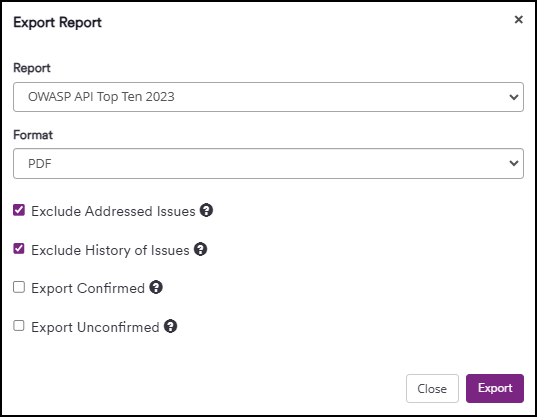
- From the Format dropdown, choose an option.
- If required, choose one of the following options to configure your report:
- Exclude addressed issues: excludes those issues you've already taken action on. (All Information level findings are marked as Accepted Risk automatically by default. To change this behavior, refer to the Do not mark Information issues as accepted risks option in General settings).
- Exclude history of issues: excludes the issue history from the report. If unselected, only the last 10 history items appear in the report. For more information, refer to the Viewing issues in Invicti Enterprise document.
- Export confirmed: includes only those issues that are confirmed.
- Export unconfirmed: includes only those issues that are unconfirmed.
- Click Export.
You can view the report in the saved location.
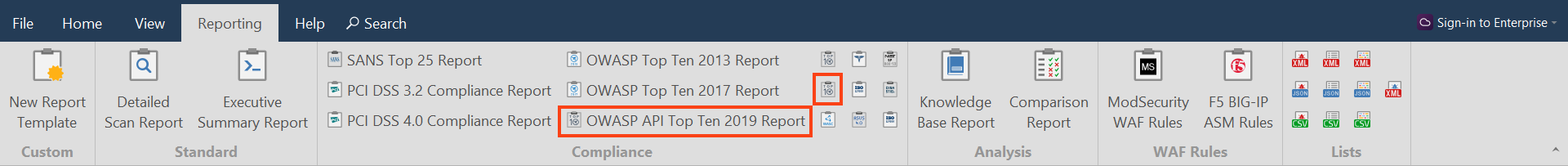
Generate an OWASP API Top Ten report in Invicti Standard
- From the File tab, choose the relevant scan from Local Scans to display its results.
- From the Reporting tab, choose OWASP API Top Ten 2019 Report or OWASP API Top Ten 2023 Report. The Save Report As dialog is displayed.
- Choose a save location, then choose Save.
- The Export Report dialog is also displayed at this point, with the Path field already populated from the previous dialog.
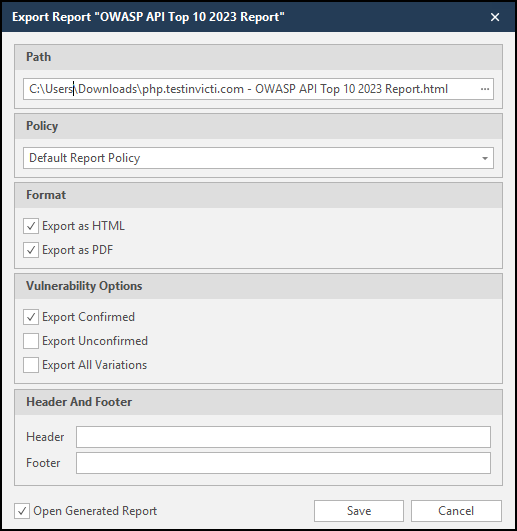
- From the Export Report dialog, you can decide on the following:
- Policy: choose the default report policy or customized report policy (refer to the Custom report policies document).
- Format: choose HTML and/or PDF format.
- Vulnerability options (choose one or all):
- Export confirmed: when selected, the report includes confirmed vulnerabilities.
- Export unconfirmed: when selected, the report also includes unconfirmed vulnerabilities.
- Export all Variations: variations mean that if Invicti identified some passive or information level issues in more than one page, it doesn't show all these variations. However, users can change this by enabling or disabling this option.
- Header and Footer: enter relevant information that appears in the header and footer section of the report.
- Open generated report: when selected, your reports are generated when you choose Save.
- Click Save.
You can view the report in the saved location.
Need help?
Invicti Support team is ready to provide you with technical help. Go to Help Center