Okta Single Sign-On integration with SAML
Okta is an identity and access management platform. Its Single Sign-On (SSO) solution allows users to log in to a variety of systems using one centralized process.
This document explains how to configure Okta and Invicti Platform for Single Sign-On.
Configure Okta with SAML
There are three steps in this process:
- Step 1: Add an application to Okta
- Step 2: Add users to the application in Okta
- Step 3: Configure auto-provisioning (optional)
Step 1: Add an application to Okta
- Navigate to Okta's Admin Console, then select Applications > Applications from the left-side menu.
- Click Create App Integration.
- From the Create a new app integration dialog, select SAML 2.0. Then click Next.

- On the Create SAML Integration page, enter a name in the App name field. Invicti is used for this example.
- Select Next.
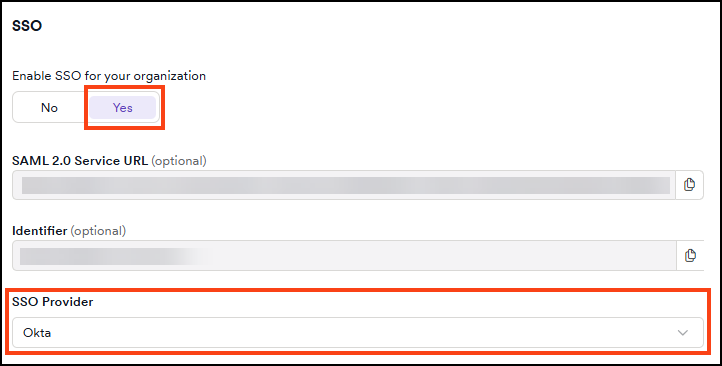
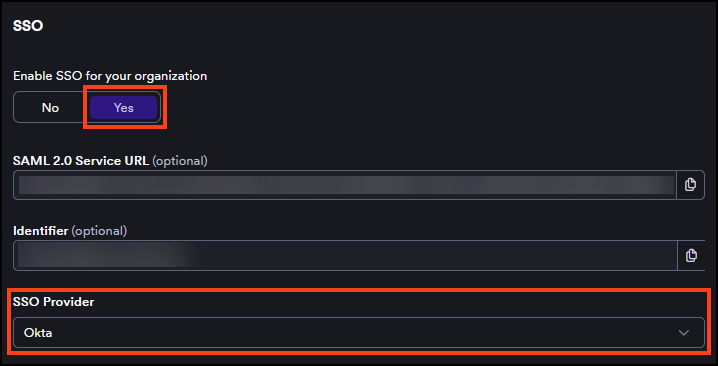
- In a new browser tab, log in to Invicti Platform and select Settings > SSO & Provisioning.
- Turn on the Enable SSO for your organization toggle.
- Select Okta from the SSO Provider drop-down list.
- Copy the SAML 2.0 Service URL and paste the URL into Okta's Single Sign-on URL field.
- Return to the Invicti browser tab and copy the Identifier URL. Paste it into Okta's Audience URI (SP Entity ID) field.
- Click Next to view the Feedback tab.
- Click Finish. The Invicti application's details appear.
- In the Sign On tab, click View SAML setup instructions. Okta opens a new browser tab.
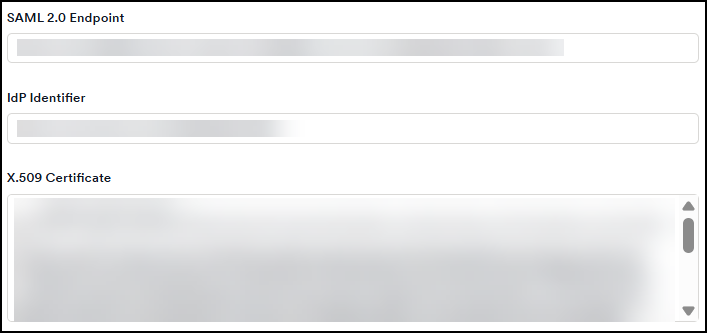
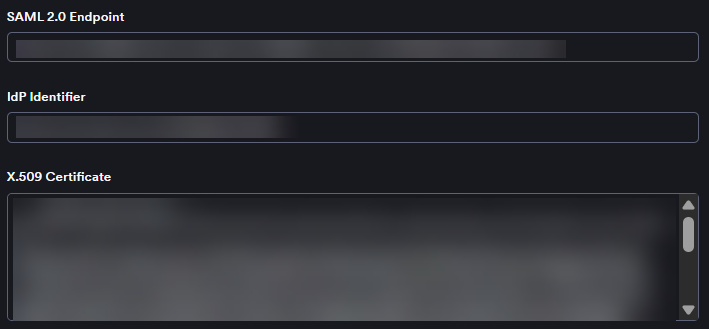
- From the new tab, copy the URL from the Identity Provider Issuer and paste the URL to Invicti's IdP Identifier field.
- In the Okta tab, copy the URL from the Identity Provider Single Sign-On URL and paste it to Invicti's SAML 2.0 Endpoint field.
- In the Okta tab, copy the content from the X.509 Certificate field. Then switch to the Invicti tab and paste the URL to the X.509 Certificate field.
- In Invicti, select the checkboxes for signed assertions, encrypted assertions, or sign requests as needed.
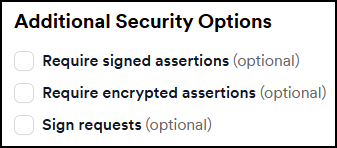
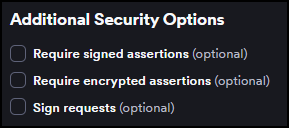
Selecting Require encrypted assertions requires applying additional settings in Okta. For instructions, refer to Configure encrypted assertions in Okta.
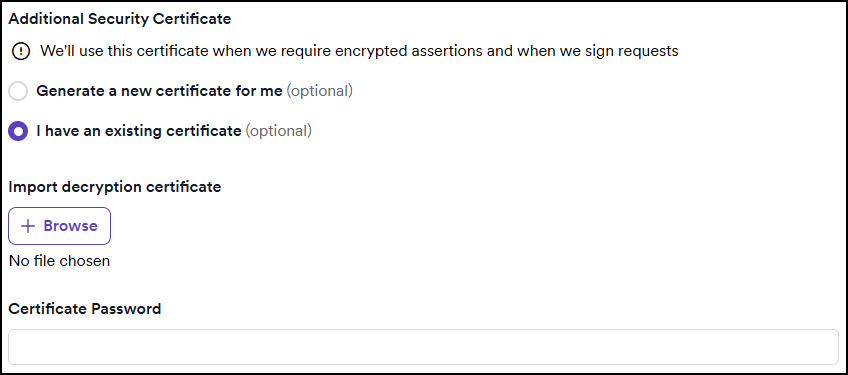
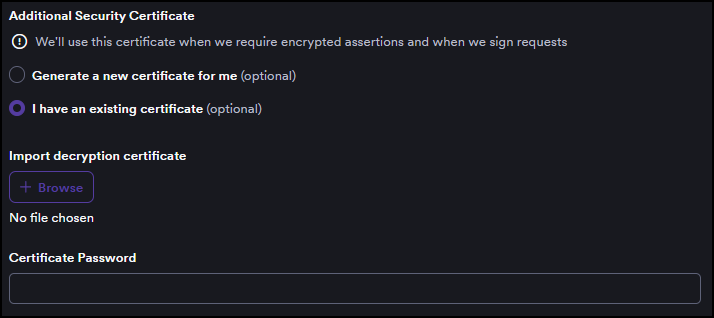
- If you enable any assertions or requests, a new section appears where you can generate a new certificate or upload an existing one.
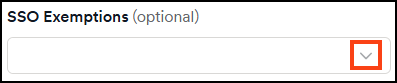
- Use the Invicti's SSO Exemptions drop-down to select users who can log in to Invicti via password.
- Click Save.
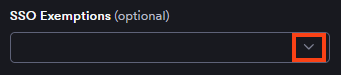
Configure encrypted assertions in Okta
- From Okta's main menu, go to Applications > Applications > Invicti.
- Select the General tab and scroll to the SAML Settings section. Click Edit.
- Click Next, then Show Advanced Settings.
- Use the drop-down next to Assertion Encryption to select Encrypted.
- Click Browse Files next to Encryption Certificate and upload your Invicti certificate.
Step 2: Add users to the application in Okta
- Select Directory > People from the left-side menu in Okta.
- Click the Add Person button to open a form.
- Fill out the form and click Save.
- Select Applications > Applications > Invicti from the menu.
- In the Assignments tab, click Assign > Assign to People.
- From the Assign Invicti to People dialog, select Assign next to the person you want to add.
- Select Save and Go Back.
- Click Done.
Users who exist in both Okta and Invicti Platform can now log in to Invicti via Okta - either by clicking the Invicti tile in the Okta dashboard (IdP-initiated) or by using the SSO option on the Invicti login page (SP-initiated). If a user doesn't yet have an Invicti account, see Step 3: Configure auto-provisioning.
Step 3: Configure auto-provisioning
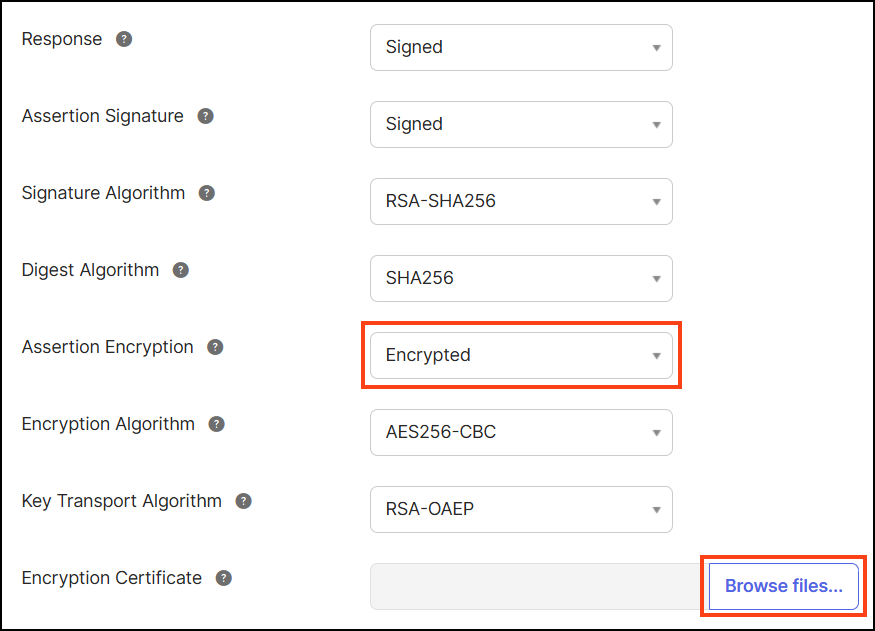
Auto-provisioning automatically creates user accounts in Invicti when users log in via Okta for the first time. To enable it, you must first add attribute statements in Okta so that Invicti receives the user's name and email, then enable provisioning in Invicti.
Add attribute statements in Okta
- In Okta, open the Invicti application and select the Sign On tab.
- In the Attribute Statements section, click Show legacy configuration, then click Edit.
- Add the following attribute statements:
| Name | Name format | Value |
|---|---|---|
FirstName | Unspecified | user.firstName |
LastName | Unspecified | user.lastName |
EmailAddress | Unspecified | user.email |
- Click Save.
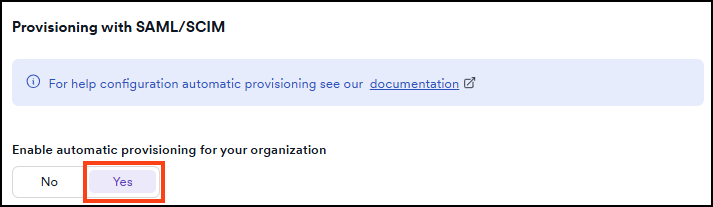
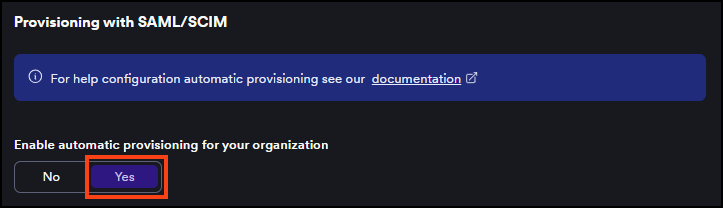
Enable auto-provisioning in Invicti
- In Invicti Platform, go to Settings > SSO & provisioning.
- In the Provisioning with SAML/SCIM section, set the Enable automatic provisioning for your organization toggle to Yes.
- In the Default access for new users and teams section, select a role from the Role drop-down to assign to newly provisioned users.
- Optionally, click Select collections to choose which collections new users can access. If none are selected, new users get access to all current and future collections by default.
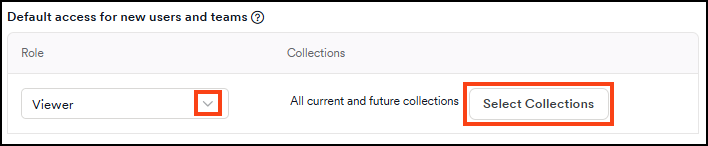
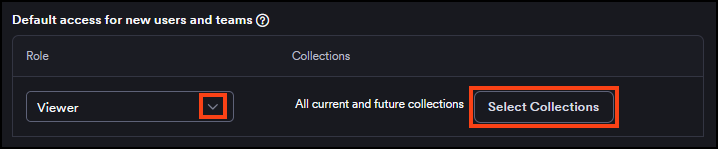
- Click Save.
For more information about SSO fields and auto-provisioning behavior, refer to the Single Sign-On configuration document.
Need help?
Invicti Support team is ready to provide you with technical help. Go to Help Center