Single Sign-On configuration
Invicti Platform supports Single Sign-On (SSO) via Security Assertion Markup Language (SAML), allowing users to access multiple applications with a single login. An Identity Provider (IdP) centralizes user and application management, eliminating the need to handle individual credentials for each service. Invicti supports both IdP- and Service Provider(SP)-initiated SAML authentication.
This document explains how to enable SSO in Invicti Platform.
Enabling SSO in Invicti doesn't automatically provision users by default. You must add them manually or use automatic provisioning with SAML/SCIM from specific SSO providers (Active Directory Federation Service, Entra ID, Google, Okta, OneLoginSecure, and PingIdentity). For more information on manual user creation, refer to the Create user document.
You must also configure the integration on your SSO provider. For detailed instructions, refer to your SSO provider's documentation in the following:
- Active Directory Federation Service
- Entra ID (Former Azure ActiveDirectory)
- Okta
- GeneralSAMLv2
- OneLoginSecure
- PingIdentity
Configure Single Sign-On settings
To access the SSO configuration you need to be an Owner of the organization or have a custom role with System rights. Enabling SSO makes it mandatory for the whole organization, unless you exempt a user.
- Select Settings from the left-side menu.
- In the Security & access control section select SSO & Provisioning.
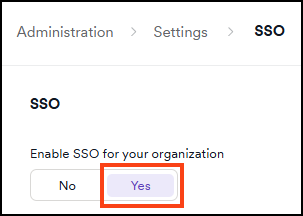
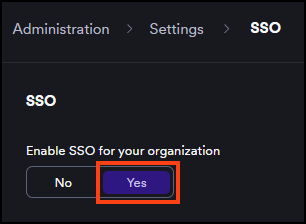
- Turn on the Enable SSO toggle.
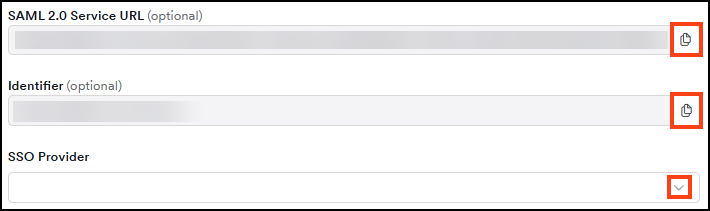
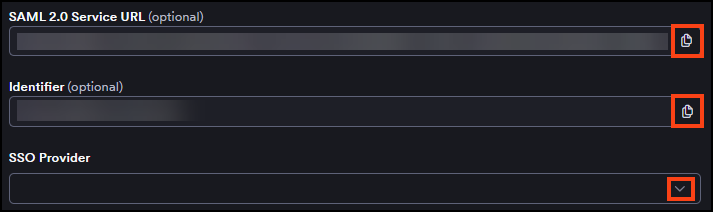
- From the SSO Provider drop-down list, choose your SSO provider.
- Copy the information from the SAML 2.0 Service URL and Identifier fields and enter it into your SSO provider configuration.
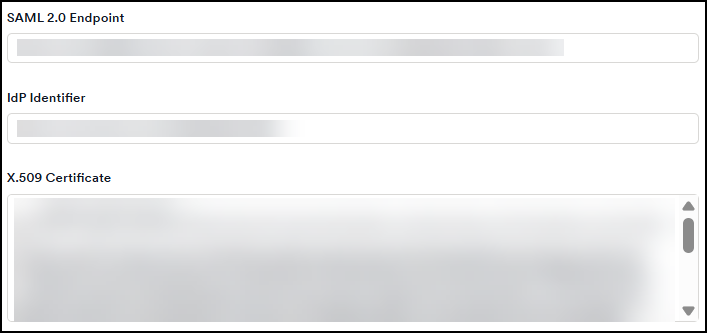
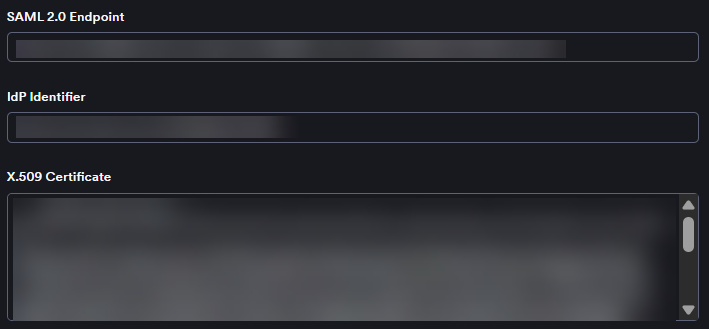
- Enter the required information into the SAML 2.0 Endpoint, IdP Identifier, and X.509 Certificate fields.
- Choose the signed assertions, encrypted assertions, or sign requests checkboxes as needed.
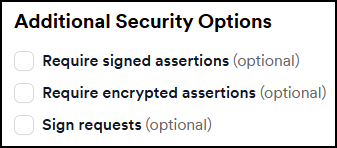
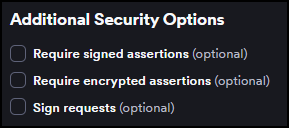
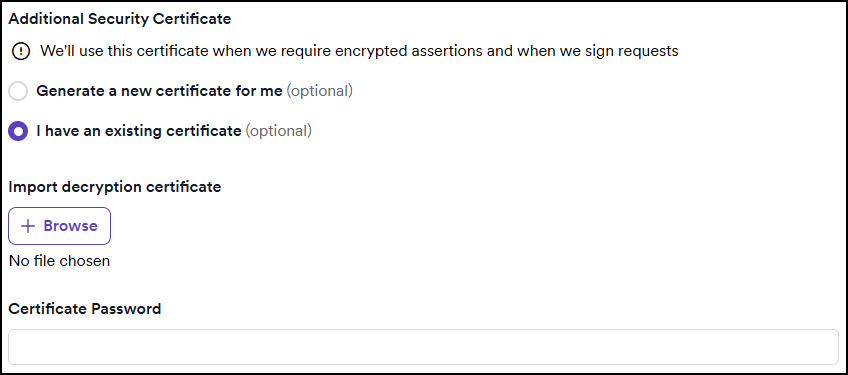
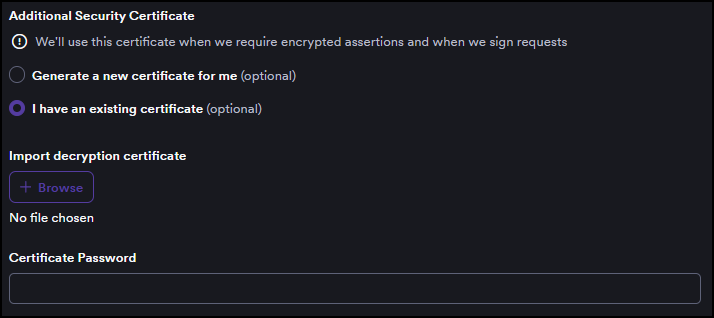
- If you enable any assertions or requests, a new section appears to do one of the following:
- Choose Generate a new certificate; OR
- Choose I have an existing certificate, then upload your certificate and enter the Certificate Password.
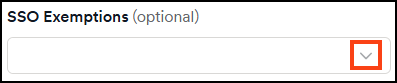
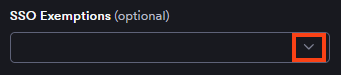
- From the SSO Exemptions drop-down, choose specific users to exempt them from SSO. Doing this means the selected users can log in to Invicti Platform using password. The Owner is always exempted, while all other users are forced to use SSO when it's enabled.
- Click Save to save your settings and add the users manually.
To add the users automatically, based on your SSO provider, continue to configure automatic provisioning section both in Invicti Platform (in the following section) and the provider's administration tool.
Configure automatic provisioning with SAML/SCIM
You need permission to manage Users to configure automatic provisioning.
Invicti Platform supports automatic user provisioning via SAML/SCIM for specific SSO providers. This feature automatically creates new user accounts when they authenticate through the Identity Provider, eliminating the need to manually add users to the platform.
Required SAML attributes
For auto-provisioning to work, your Identity Provider must send the following attributes in the SAML assertion:
| Attribute | Description | Expected format |
|---|---|---|
EmailAddress | User's email address | Plain string |
FirstName | User's first name | Plain string |
LastName | User's last name | Plain string |
If any required attributes are missing from the SAML assertion, Invicti rejects the login and doesn't create a user.
Configure provisioning settings
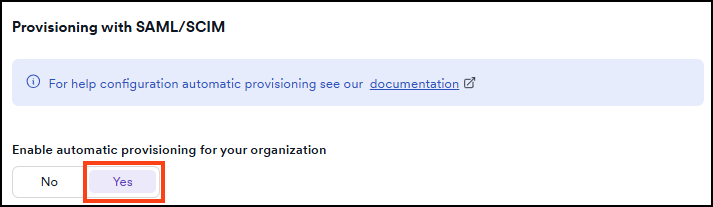
- In the Provisioning with SAML/SCIM section, set the Enable automatic provisioning for your organization toggle to Yes.
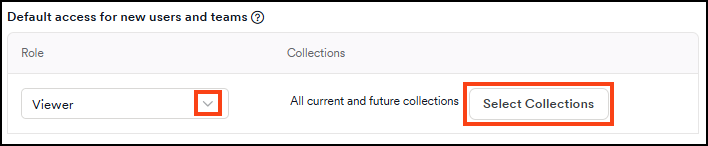
- In the Default access for new users and teams section, select a role from the Role drop-down to assign to newly provisioned users.
- Optionally, click Select collections to choose which collections the new users can access. If none are selected, new users get access to all current and future collections by default.
- Optionally, click Download SAML Metadata to download the file for your IdP configuration.
- Click Save to apply your provisioning settings.
Once you enable automatic provisioning, Invicti Platform automatically creates accounts for new users who successfully authenticate through your Identity Provider, with the default role and collection access you configured.
To change a user's first name, last name, and email edit their profile in your Identity Provider. To edit a user's role and access to collections, refer to the Edit, delete, or suspend user document.
Auto-provisioning behavior
When a user authenticates through your Identity Provider, Invicti Platform handles the request based on the following conditions:
| Condition | Outcome |
|---|---|
| User with matching email already exists in the tenant | User is logged in. Email matching is case-insensitive. No duplicate account is created. |
| User doesn't exist in the tenant | New user account is created with the default role configured in Default access for new users and teams. |
| Required SAML attributes are missing | Login is rejected. No user is created. Error message "We encountered some issue with SSO login, please contact your administrator (and check whether e.g. configuration/certificate is still valid.)" is displayed. |
| Auto-provisioning is disabled | Login is denied for users who don't have an existing account. No user is created. |
Need help?
Invicti Support team is ready to provide you with technical help. Go to Help Center