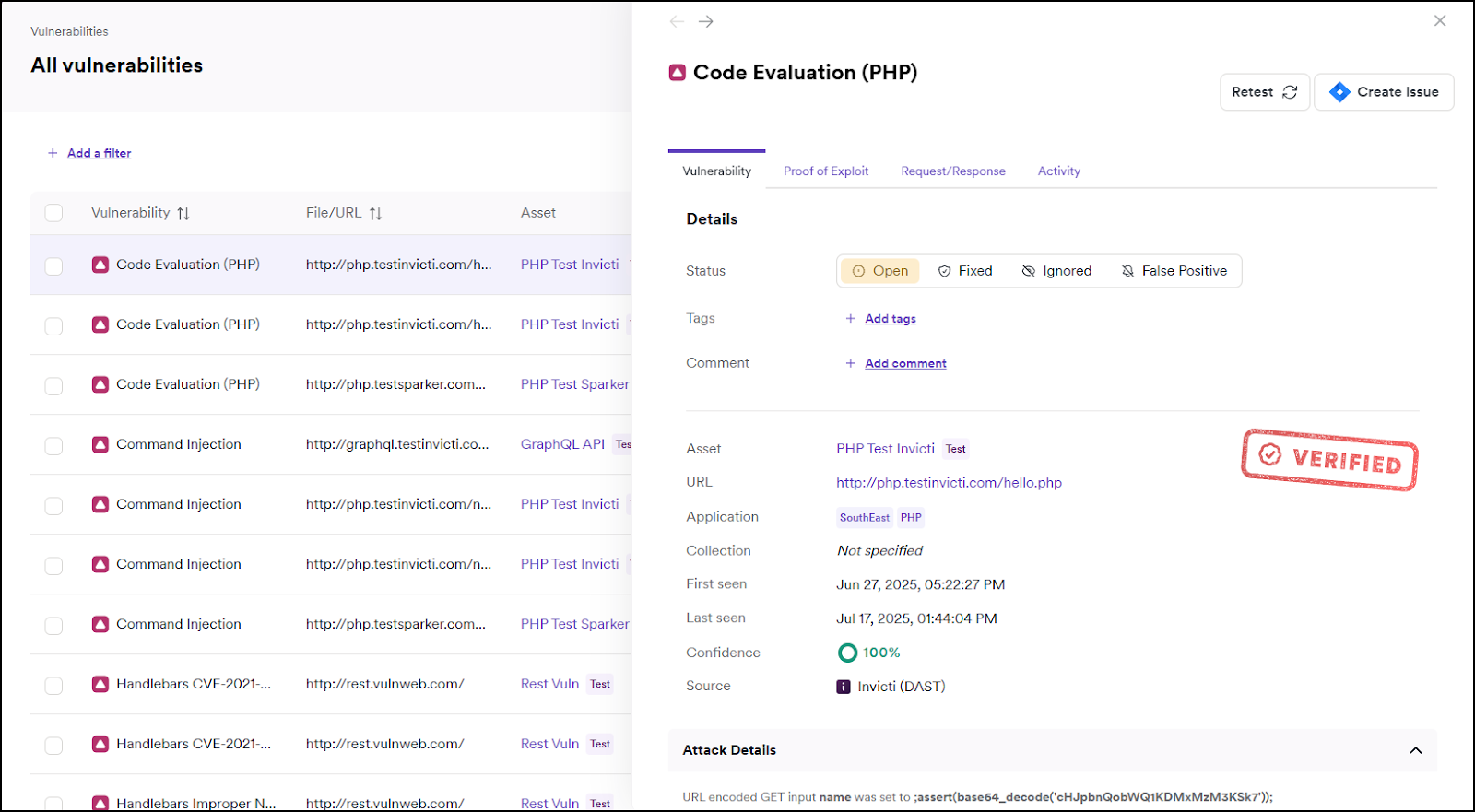
View vulnerability details
When you select a vulnerability, Invicti Platform provides comprehensive information, including attack details and potential impact. These vulnerability details help you understand the core cause of the vulnerability, assess the severity of the issue, and determine how urgently it needs to be addressed.
This document provides a high-level explanation of the information available on the Vulnerabilities page when viewing the details of a vulnerability.
View vulnerability details
Vulnerability details can be accessed from the Vulnerabilities page or the Vulnerabilities section when reviewing scan results.
When you select a vulnerability from the list, its details appear on the right-hand side. The information provided for each vulnerability is explained in the following section.
What information is provided?
DAST vulnerability details can contain the following sections:
Information provided for vulnerabilities found by SAST, SCA, or Container scan might be different.
Vulnerability tab
Summary section:
- Status of the vulnerability: Open or Rediscovered, Fixed (Unconfirmed) or Fixed, Ignored, or False Positive. For more information on statuses, refer to the Vulnerabilities overview document.
- Assignee: the user name of the person to whom the vulnerability is assigned.
- Comment: comment related to the vulnerability.
- Tags: tags assigned to the vulnerability.
- Issue URL: link to the vulnerability in the integrated issue tracker.
Details section:
- Vulnerability ID: ID of the vulnerability.
- Asset: the target where the vulnerability was identified.
- URL: the link to the resource that contains the issue.
- Application: application with the target. For more information on applications refer to the What is an application document.
- Collection: collection with the target. For more information on collections, refer to the What is a collection document.
- Severity: displays the severity level and notes if the default level has been modified. For more information on severity level changes, refer to the Change vulnerability severity document.
- First seen: the date and time when the vulnerability was first identified by Invicti.
- Last seen: the date and time when the vulnerability was last identified by Invicti.
- Confidence: lists the confidence level, showing how certain Invicti is of the vulnerability it identified.
- Source: displays how the vulnerability was identified - either through DAST, SAST, SCA or Container Security scan results.
Attack details section:
- Attack Details: whenever possible provides the information about the attack parameters and variables Invicti used to exploit the vulnerability. For example, a Cross Site Scripting alert shows the name of the exploited input variable and the string it was set to.
Vulnerability description section:
- Vulnerability Description: more detailed description to help you understand the vulnerability.
The impact of this vulnerability_ section:
- The impact of this vulnerability: this shows the effect of the vulnerability on the target URL if this vulnerability is exploited.
How to fix this vulnerability section:
- How to fix this vulnerability: guidance on how to fix the vulnerability.
Classification section:
- Classification: listing of the Common Weakness Enumeration (CWE) ID and Common Vulnerability Scoring System (CVSS) - v3.0 and v4.0 scores to provide an idea of how severe the vulnerability is on a global scale. CWE also includes the link to the relevant CWE web page. CVSS provides the Base Score and vector string: Attack Vector, Attack Complexity, Privileges Required, User Interaction, Scope, Confidentiality, Integrity, and Availability.
Web references section:
- Web references: a list of web links to external sources providing more information on the vulnerability to help you understand and fix it.
Compliance section:
- Compliance: a list of compliance standards and specific control IDs associated with the detected vulnerability. For example,
ISO27001 - 12-5.1for Handlebars Improper Control of Generation of Code vulnerability.
All users can view the Compliance section in the vulnerability details. This section is independent of the permission required to generate compliance reports.
Proof of Exploit tab
This section provides detailed evidence information on vulnerabilities that were verified by Invicti Platform. The proof of exploit confirms the severity of the vulnerability by providing information that's considered confidential and shouldn't be accessible.
If you enable IAST sensor, you can have more information about the proof and vulnerability. Invicti IAST shows the exact location of the issue and simplifies remediation efforts.
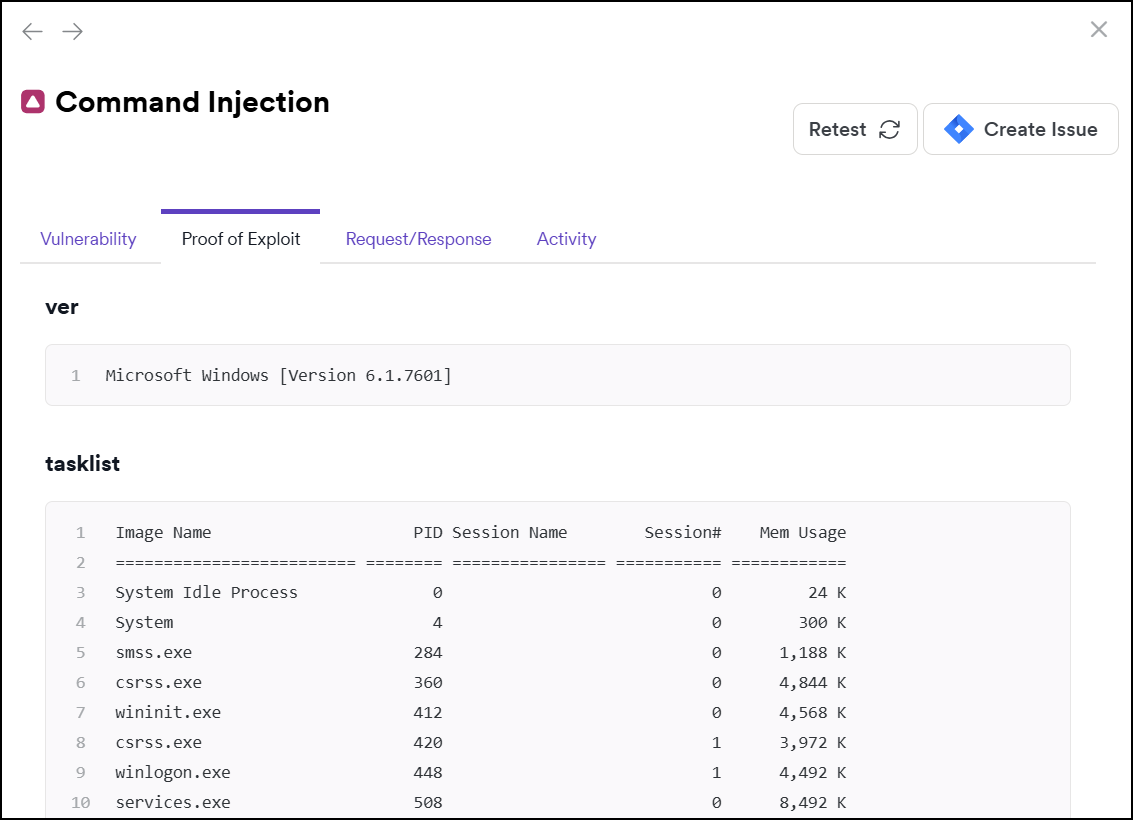
Proof of Exploit information isn't available for all vulnerabilities.
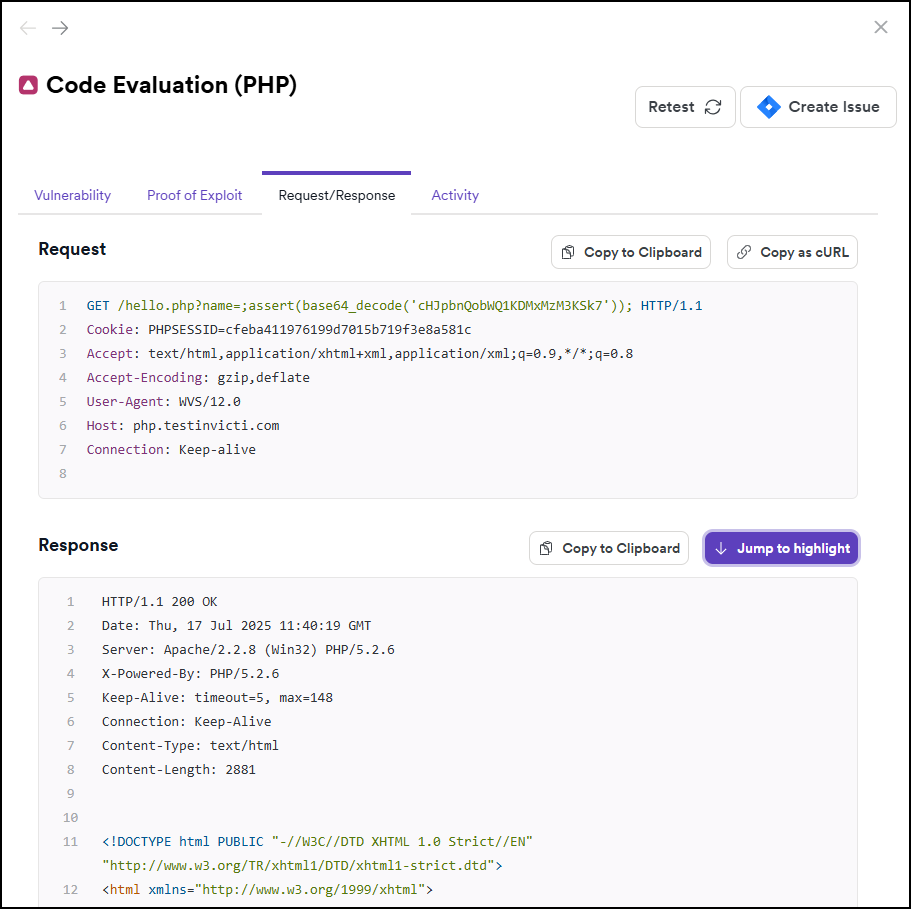
Request/Response tab
- Request: the whole HTTP request that Invicti sent to detect the issue. This request helps you understand how the scanner exploited the vulnerability.
- Response: the reply from the system against the payload. Invicti highlights the vulnerability section in the response.
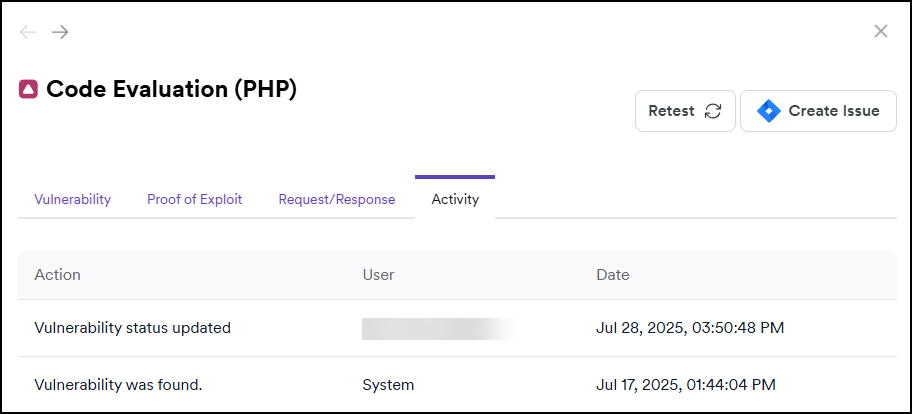
Activity tab
This section provides information on the activity related to the vulnerability, for example, change of the vulnerability’s status.
Need help?
Invicti Support team is ready to provide you with technical help. Go to Help Center