Package: Invicti AppSec Enterprise (on-premise, on-demand)
Checkmarx One SAST Integration
Invicti AppSec supports Checkmarx One SAST as a SAST (Static Application Security Testing) scanner. This guide explains how to activate and configure the Checkmarx One SAST integration.
Checkmarx One is a unified application security platform that provides comprehensive SAST scanning across multiple programming languages.
Prerequisites
Before starting the integration, ensure you have the following information from your Checkmarx One account:
| Field | Description | Required |
|---|---|---|
| Token | OAuth Refresh Token generated from your Checkmarx One IAM | Yes |
| URL | Your Checkmarx One IAM URL (e.g., https://<region>.iam.checkmarx.net) | Yes |
| Tenant Name | Your Checkmarx One tenant name | Yes |
| Insecure | Skip SSL certificate verification (not recommended for production) | No |
How to Get a Refresh Token (on Checkmarx One Side)
- Log in to the Checkmarx One portal.
- Navigate to Identity & Access Management (IAM).
- Go to API Keys section.
- Click Generate API Key.
- Copy the generated refresh token and save it securely.
Step 1: Navigate to Integrations
From the left sidebar menu, click on Integrations.
Step 2: Select the SAST Tab
On the Integrations page, you will see the Scanners section with multiple tabs. Click on the SAST tab (it is selected by default).
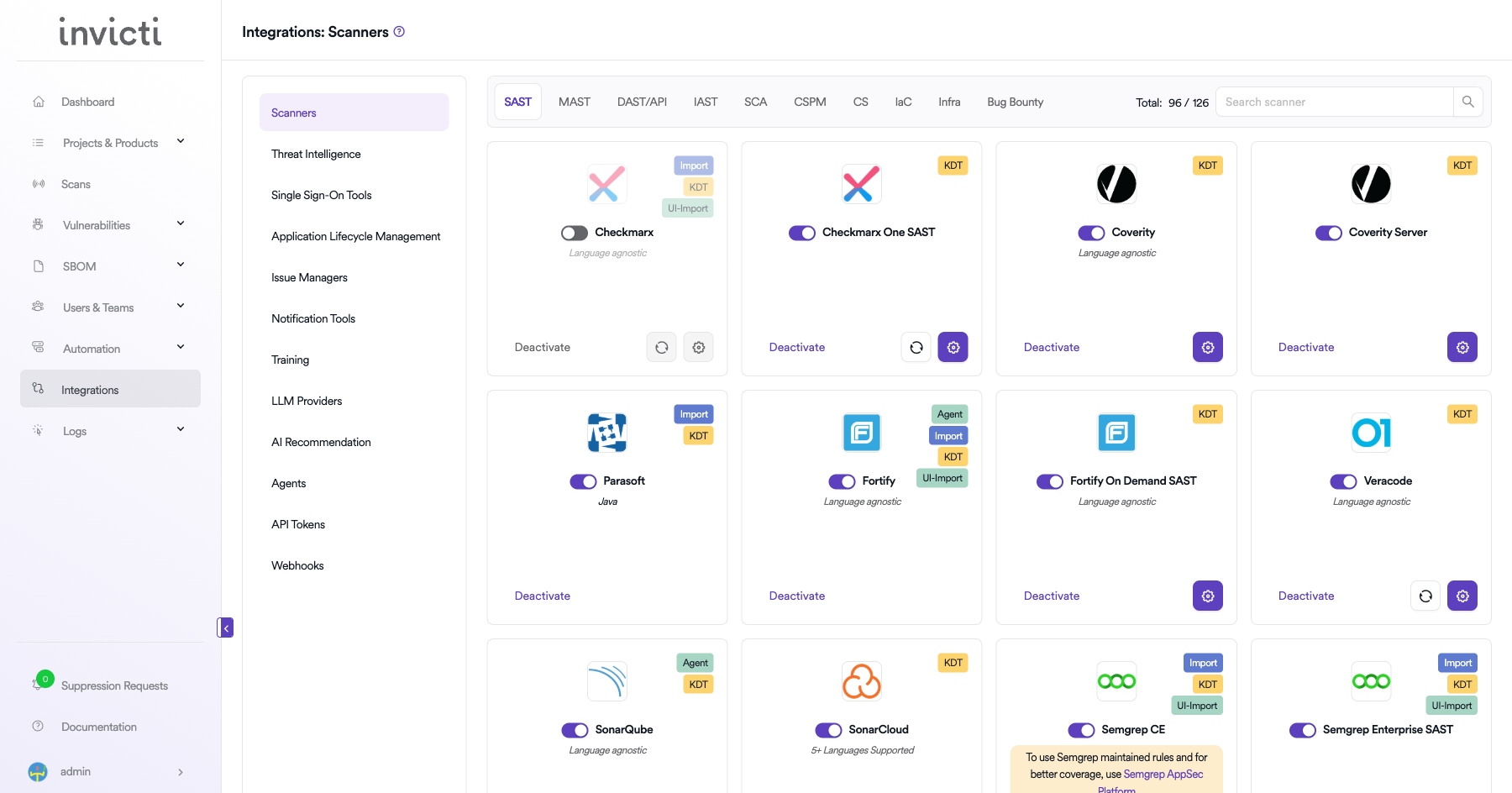
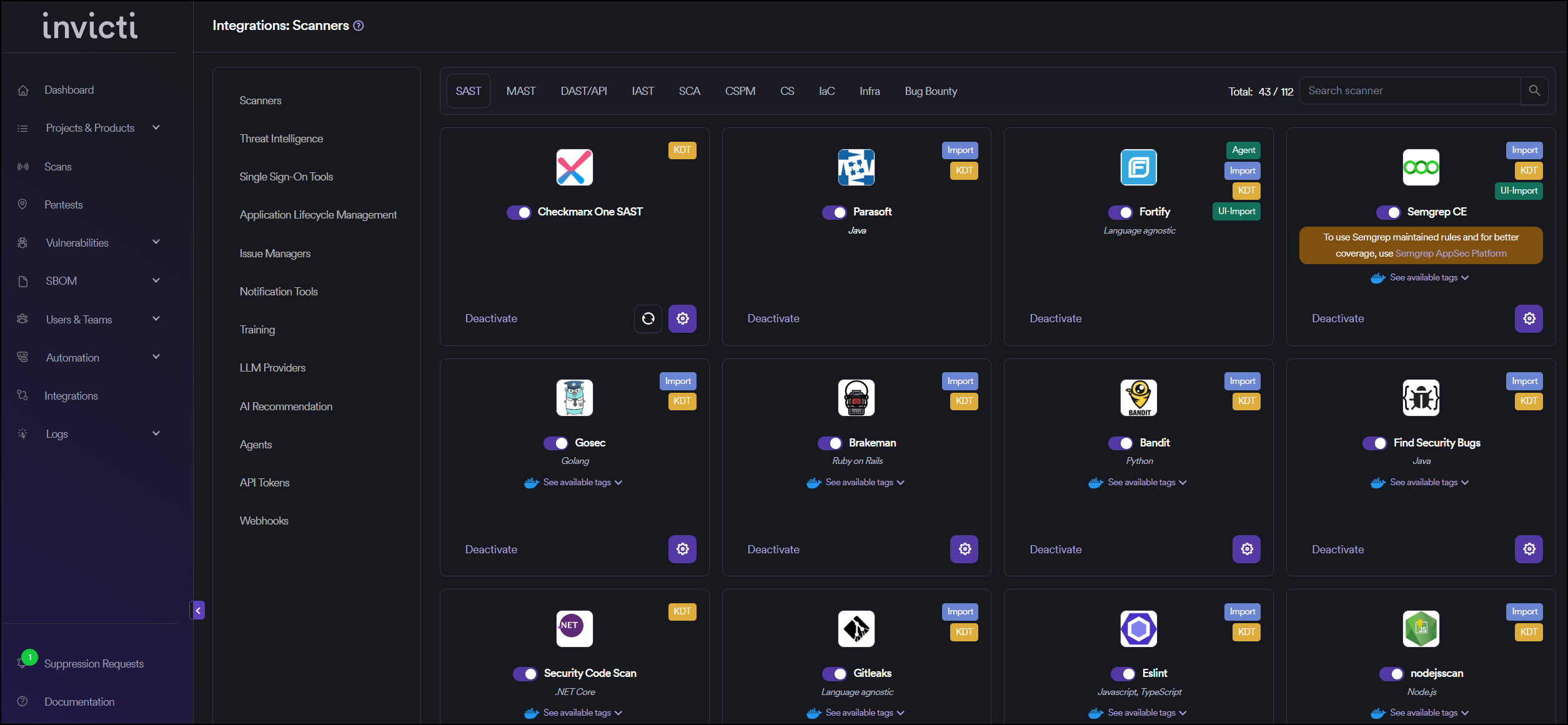
Step 3: Find and Activate Checkmarx One SAST
Scroll through the list of SAST scanners to find Checkmarx One SAST.
- If Checkmarx One SAST is not activated, you will see an "Activate" button. Click it to enable the integration.
- If Checkmarx One SAST is already activated, you will see a toggle switch in the ON position and a "Deactivate" button, along with a gear icon for configuration.
The scan method badge on the Checkmarx One SAST card shows KDT, which means scans are triggered through the Kondukto CLI tool (KDT).
:::
Step 4: Configure Connection Settings
Click on the gear icon on the Checkmarx One SAST card to open the configuration panel. Fill in the required fields:
- Token: Paste the OAuth refresh token you generated from Checkmarx One IAM.
- Tenant Name: Enter your Checkmarx One tenant name.
- URL: Enter your Checkmarx One IAM URL (e.g.,
https://eu.iam.checkmarx.net). - Insecure: Enable this checkbox only if your Checkmarx One instance uses a self-signed SSL certificate.
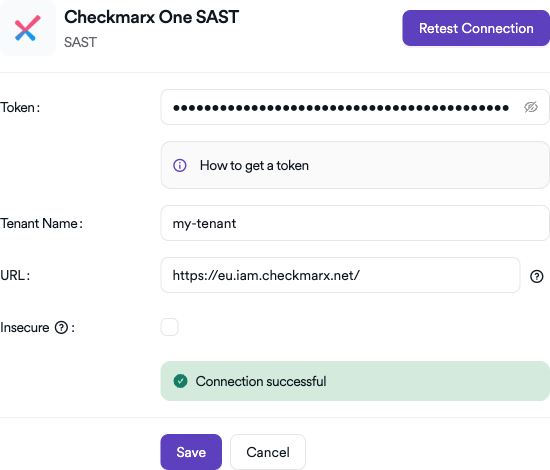
Step 5: Test the Connection
Click the "Test Connection" button at the bottom of the configuration panel to verify that the provided credentials and URL are correct.
- If the connection is successful, the integration is ready to use.
- If the connection fails, verify your refresh token, URL, and tenant name values.
- For existing integrations, you can use the "Retest Connection" button at the top of the panel.
Step 6: Advanced Settings (Optional)
Click on "Advanced Settings" to expand additional options:
| Setting | Description | Default |
|---|---|---|
| Allow team leads to scan this instance | Permits team leads to trigger scans using this Checkmarx One instance | Off |
| Allow team leads to create new instances | Permits team leads to create additional Checkmarx One instances | Off |
After modifying advanced settings, click "Save Advanced Settings" to apply changes.
Summary
| Step | Action |
|---|---|
| 1 | Navigate to Integrations from the sidebar |
| 2 | Select the SAST tab under Scanners |
| 3 | Find Checkmarx One SAST and click Activate (if not already active) |
| 4 | Click the gear icon and fill in Token, Tenant Name, and URL |
| 5 | Click Test Connection to verify |
| 6 | (Optional) Configure Advanced Settings for team lead permissions |
How to Create a Scan
After activating and configuring Checkmarx One SAST, you can create scans from your project's scanner settings.
Navigate to Project Scanners
- Go to your Project page.
- Click on the Settings tab.
- Select Scanners from the left sidebar.
Add Checkmarx One SAST Scanner
- In the scanner type dropdown, select SAST.
- In the scanner dropdown, search for and select Checkmarx One SAST.
- Click the Add button to open the scan configuration drawer.
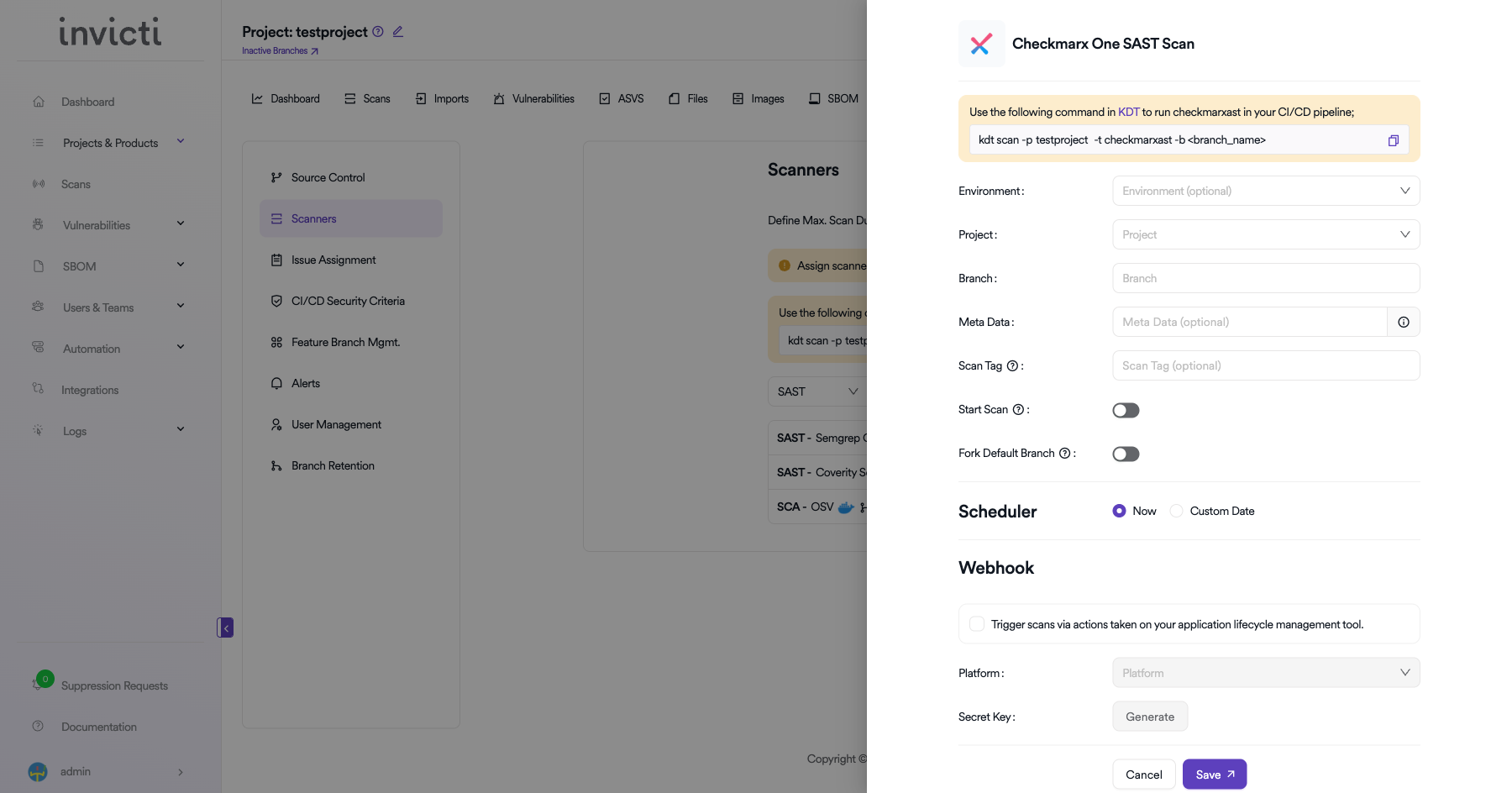
Scan Configuration Fields
| Field | Description | Required |
|---|---|---|
| Environment | Select the environment for the scan (optional) | No |
| Project | Select the Checkmarx One project to bind to | Yes |
| Branch | Specify the branch to scan | No |
| Meta Data | Additional metadata for the scan (optional) | No |
| Scan Tag | Tag to identify the scan (optional) | No |
| Start Scan | Toggle to start the scan immediately on Checkmarx side | No |
| Fork Default Branch | Enable to fork the default branch before scanning | No |
Scheduler
- Now: Run the scan immediately after saving.
- Custom Date: Schedule the scan for a specific date and time.
Webhook (Optional)
Enable webhook to trigger scans via actions taken on your application lifecycle management tool:
- Check the Trigger scans via actions checkbox.
- Select the Platform (e.g., GitHub, GitLab, Bitbucket).
- Click Generate to create a Secret Key for webhook authentication.
KDT Command
You can also trigger Checkmarx One SAST scans from your CI/CD pipeline using KDT:
kdt scan -p <project_name> -t checkmarxast -b <branch_name>
Click Save to create the scan configuration.
Troubleshooting
Connection Fails
- Invalid Token: Ensure the OAuth refresh token is correct and has not expired. Generate a new refresh token from the Checkmarx One IAM portal.
- Wrong Tenant Name: Verify the tenant name matches your Checkmarx One account exactly.
- Incorrect URL: Ensure the URL matches your Checkmarx One region (e.g.,
https://eu.iam.checkmarx.net/for EU,https://nam.iam.checkmarx.net/for North America). - SSL Certificate Issues: If using a self-hosted instance, enable the Insecure checkbox for self-signed certificates.
Scan Issues
- No Projects Found: Verify the token has sufficient permissions to list projects in Checkmarx One.
- Scan Timeout: Large codebases may take longer to scan. Monitor scan status on the Checkmarx One dashboard.
- Preset Not Found: Ensure the selected scan preset exists in your Checkmarx One account.
Best Practices
- Use Service Account Tokens: Create a dedicated service account in Checkmarx One for the Invicti AppSec integration.
- Rotate Tokens Regularly: OAuth refresh tokens should be rotated periodically as part of security hygiene.
- Select Correct Region: Ensure you are using the correct IAM URL for your Checkmarx One deployment region.
- Use Specific Presets: Select appropriate scan presets to optimize scan time and result quality.
Limitations
- Region-Specific URLs: Each Checkmarx One region has its own IAM endpoint. Using the wrong region URL will cause authentication failures.
- OAuth Flow: The integration uses OAuth refresh tokens, which may have different expiration policies than API keys.
- Scan Presets: Available scan presets depend on your Checkmarx One subscription level and configuration.
Need help?
Invicti Support team is ready to provide you with technical help. Go to Help Center