Package: Invicti AppSec Core (on-demand), Invicti AppSec Enterprise (on-premise, on-demand)
Fortify On Demand DAST Integration
Fortify On Demand (FoD) is Micro Focus's cloud-based security testing platform that provides dynamic application security testing as a service. This integration allows Invicti AppSec to trigger Fortify On Demand DAST scans and import vulnerability findings.
Prerequisites
| Field | Description |
|---|---|
| API URI | Fortify On Demand API base URI (e.g., https://api.ams.fortify.com) |
| Client ID | The client ID from your Fortify On Demand API credentials |
| Client Secret | The client secret from your Fortify On Demand API credentials |
Get API Credentials (on Fortify On Demand Side)
- Log in to the Fortify On Demand Portal.
- Navigate to Administration > Settings > API.
- Click Add Key to generate a new API key pair.
- Enter a name for the key and select the required scopes (at minimum:
api-tenant,dynamic-scan:read,dynamic-scan:start). - Copy the Client ID and Client Secret — the secret is shown only once.
Step 1: Navigate to Integrations
From the left sidebar menu, click on Integrations.
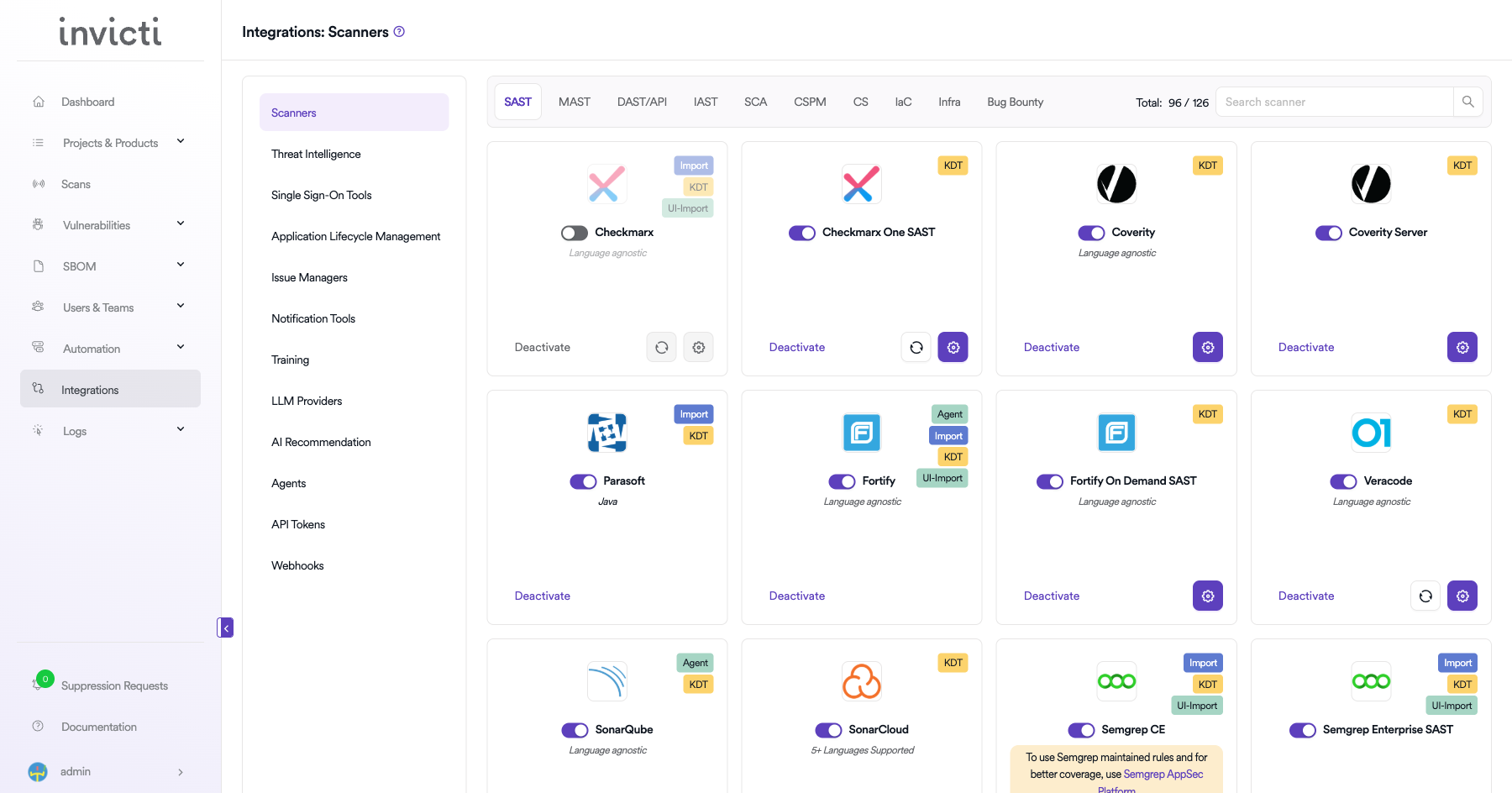
Step 2: Select the DAST/API Tab
On the Integrations > Scanners page, click on the DAST/API tab.
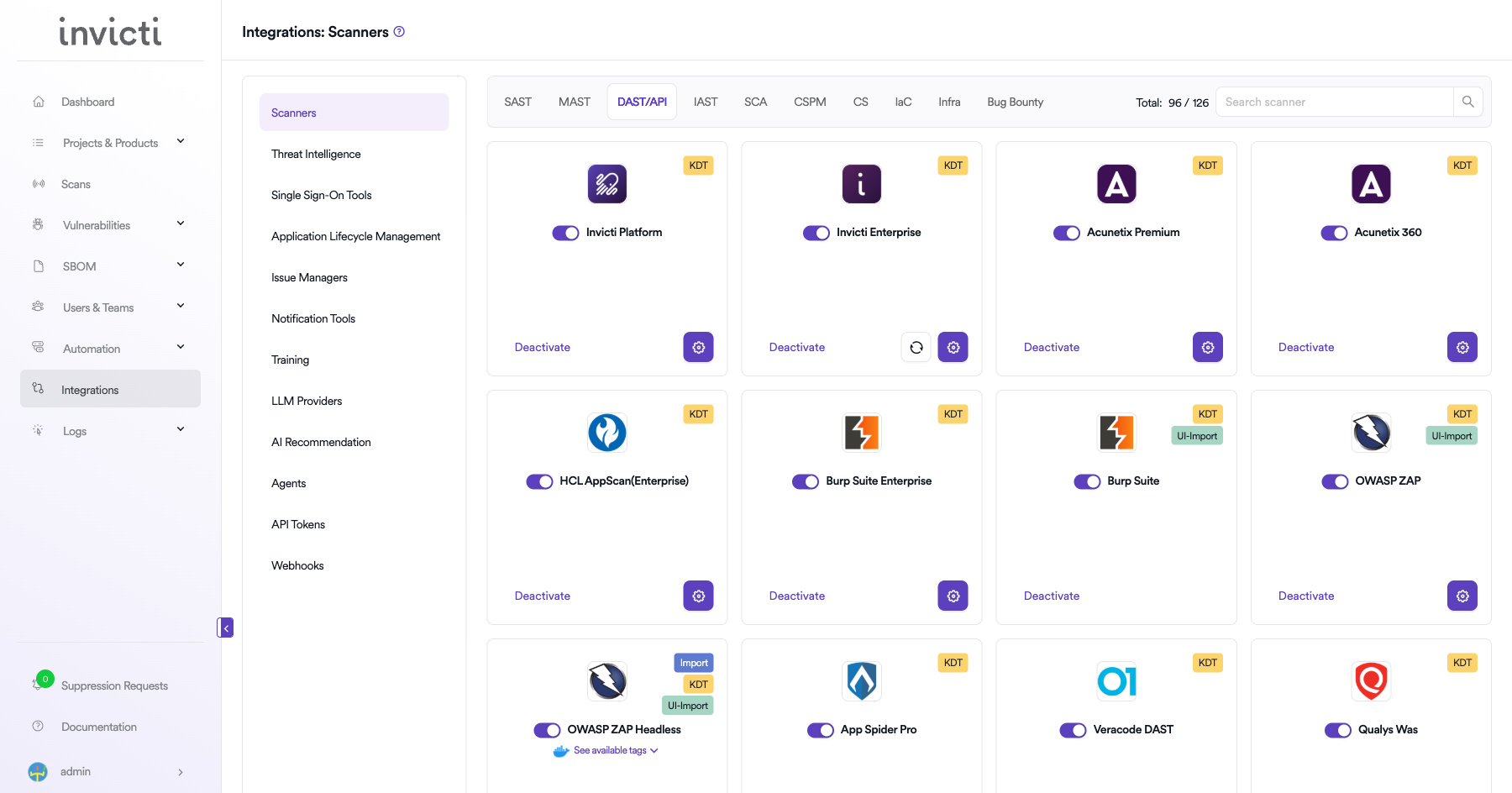
Step 3: Find and Activate Fortify On Demand DAST
Scroll through the list of DAST/API scanners to find Fortify On Demand DAST.
- If Fortify On Demand DAST is not activated, you will see an "Activate" button. Click it to enable the integration.
The scan method badge on the Fortify On Demand DAST card shows KDT, which means scans are triggered through the Kondukto CLI tool (KDT).
Step 4: Configure Connection Settings
Click on the gear icon on the Fortify On Demand DAST card to open the configuration panel. Fill in the required fields:
- Client ID: Enter your FoD API client ID.
- Secret Key: Paste your FoD API client secret key.
- URL: Enter the Fortify On Demand API URL for your region (e.g.,
https://api.ams.fortify.com). - Insecure: Enable this checkbox only if your Fortify On Demand instance uses a self-signed SSL certificate.
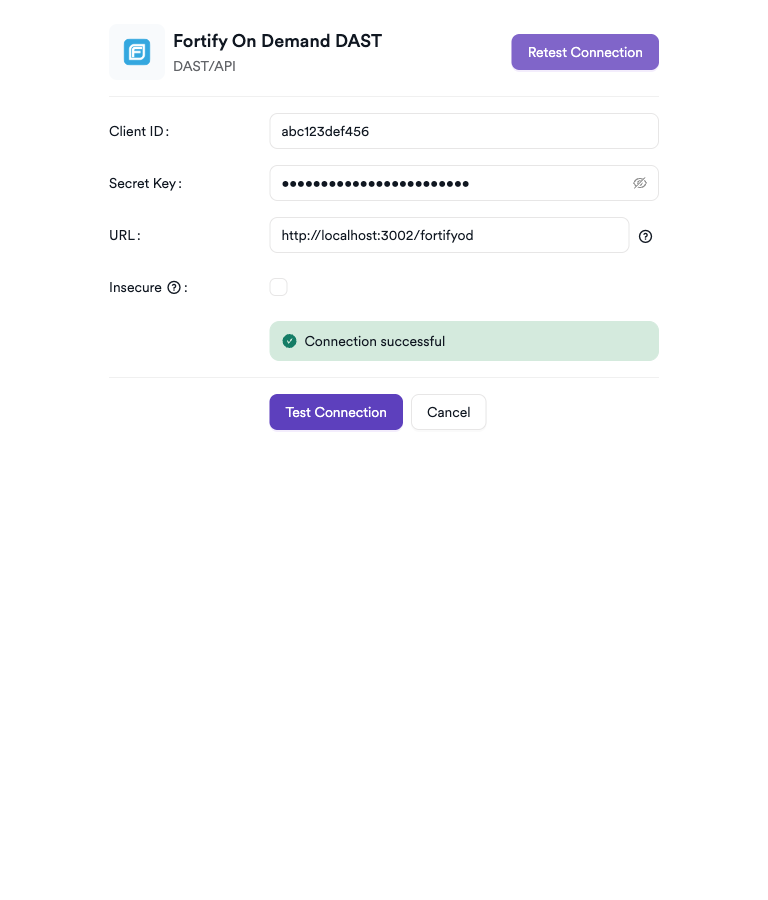
Step 5: Test the Connection
Click Test Connection. A green Connection successful message confirms valid credentials.
Summary
| Step | Action |
|---|---|
| 1 | Navigate to Integrations from the sidebar |
| 2 | Select the DAST/API tab |
| 3 | Activate Fortify On Demand DAST |
| 4 | Enter API URI, Client ID, and Client Secret |
| 5 | Test the connection |
Create a Scan
Navigate to Project Scanners
- Open a project in Invicti AppSec.
- Go to Settings > Scanners.
- Click Add Scanner.
Add Fortify On Demand DAST Scanner
- Select DAST/API as the scanner type.
- Choose Fortify On Demand DAST from the scanner list.
- Click Add to open the scan configuration drawer.
Scan Configuration Fields
| Field | Description | Required |
|---|---|---|
| Environment | Select the environment for the scan | No |
| Bind To | Fortify On Demand project to bind to | Yes |
| Profiles | Scan profile to use | No |
| Branch | Source code branch associated with this scan | No |
| Meta Data | Additional metadata for the scan | No |
| Scan Tag | Tag to identify the scan | No |
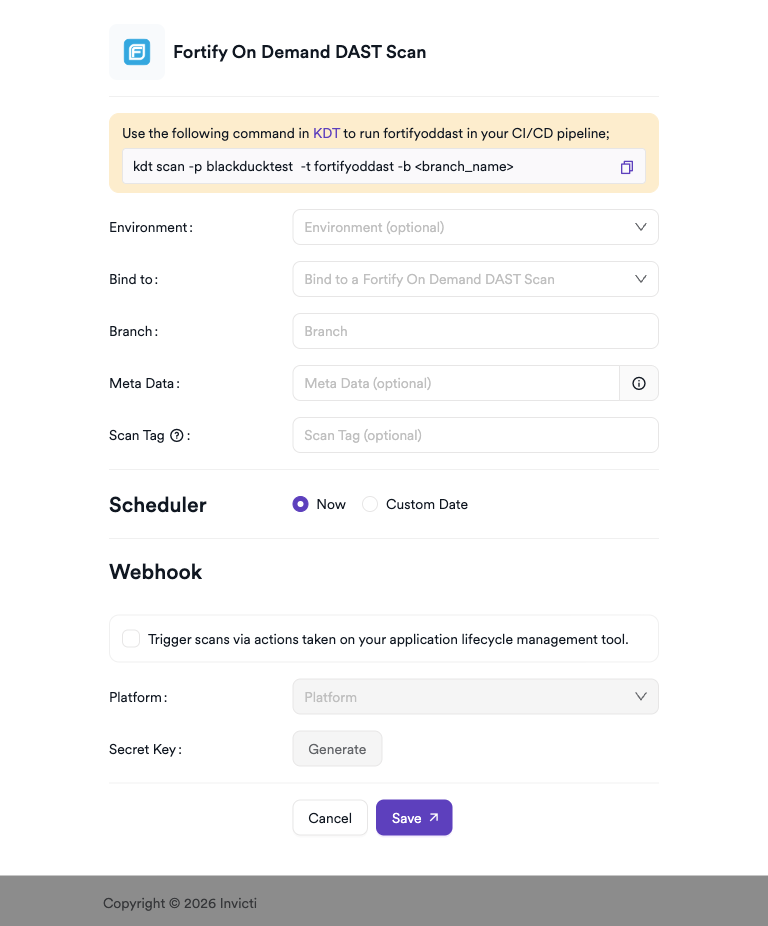
Scheduler
Enable the Scheduler toggle to run scans on a recurring schedule.
Webhook (Optional)
Add a webhook URL to receive scan completion notifications.
KDT Command
kdt scan -p <project_name> -t fodast -b <branch_name>
Troubleshooting
Connection Fails
| Issue | Resolution |
|---|---|
| Invalid client credentials | Regenerate API credentials from the FoD portal and update the integration |
| Wrong API URI | Confirm the API URI for your region (AMS: api.ams.fortify.com, EMEA: api.emea.fortify.com, APAC: api.apac.fortify.com) |
| Insufficient scopes | Recreate the API key with the required scopes for dynamic scanning |
| Network access | Ensure Invicti AppSec can reach the Fortify On Demand API endpoints on port 443 |
Scan Issues
| Issue | Resolution |
|---|---|
| No applications listed | Verify the API credentials have access to the target FoD applications |
| Scan not starting | Check FoD scan entitlement availability for your subscription |
| Empty results | Confirm the scan completed in the FoD portal and results are available |
| Entitlement exhausted | Contact Fortify On Demand support to review scan entitlement consumption |
Best Practices
- Use dedicated API credentials scoped to only the required permissions.
- Select the correct region-specific API URI to avoid connection failures.
- Rotate client secrets periodically and update the integration promptly.
- Ensure FoD applications and releases are pre-configured before triggering scans.
- Monitor scan entitlement consumption to avoid running out of allocated scan units.
Limitations
- The API URI is region-specific; using the wrong URI will result in authentication failures.
- Scan availability depends on your FoD subscription entitlement (number of scan units).
- Applications and releases must be pre-created in the FoD portal; they cannot be managed from Invicti AppSec.
- Some DAST scan options (e.g., authenticated scan setup, network authentication) must be configured directly in the FoD portal.
Need help?
Invicti Support team is ready to provide you with technical help. Go to Help Center